- Programming
- Virtualization
- Productivity

Understanding User Rights Assignment - How to lock down or unlock your user's actions

Final notes
- https://www.experts-exchange.com/articles/3360/Understanding-User-Rights-Assignment-How-to-lock-down-or-unlock-your-user's-actions.html copy
- Active Directory
Comments (1)

Have a question about something in this article? You can receive help directly from the article author. Sign up for a free trial to get started.
The Original Tech Community
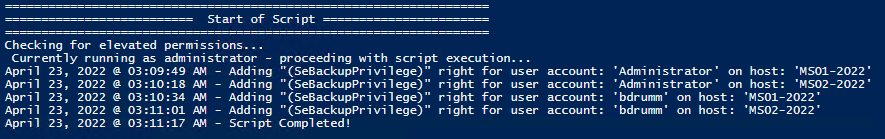
Set and Check User Rights Assignment via Powershell
You can add, remove, and check user rights assignment (remotely / locally) with the following powershell scripts..
Posted by : blakedrumm on Jan 5, 2022
Local Computer
Remote computer, output types.
This post was last updated on August 29th, 2022
I stumbled across this gem ( weloytty/Grant-LogonAsService.ps1 ) that allows you to grant Logon as a Service Right for a User. I modified the script you can now run the Powershell script against multiple machines, users, and user rights.
Set User Rights
How to get it.
All of the User Rights that can be set:
| Privilege | PrivilegeName |
|---|---|
| SeAssignPrimaryTokenPrivilege | Replace a process level token |
| SeAuditPrivilege | Generate security audits |
| SeBackupPrivilege | Back up files and directories |
| SeBatchLogonRight | Log on as a batch job |
| SeChangeNotifyPrivilege | Bypass traverse checking |
| SeCreateGlobalPrivilege | Create global objects |
| SeCreatePagefilePrivilege | Create a pagefile |
| SeCreatePermanentPrivilege | Create permanent shared objects |
| SeCreateSymbolicLinkPrivilege | Create symbolic links |
| SeCreateTokenPrivilege | Create a token object |
| SeDebugPrivilege | Debug programs |
| SeDelegateSessionUserImpersonatePrivilege | Obtain an impersonation token for another user in the same session |
| SeDenyBatchLogonRight | Deny log on as a batch job |
| SeDenyInteractiveLogonRight | Deny log on locally |
| SeDenyNetworkLogonRight | Deny access to this computer from the network |
| SeDenyRemoteInteractiveLogonRight | Deny log on through Remote Desktop Services |
| SeDenyServiceLogonRight | Deny log on as a service |
| SeEnableDelegationPrivilege | Enable computer and user accounts to be trusted for delegation |
| SeImpersonatePrivilege | Impersonate a client after authentication |
| SeIncreaseBasePriorityPrivilege | Increase scheduling priority |
| SeIncreaseQuotaPrivilege | Adjust memory quotas for a process |
| SeIncreaseWorkingSetPrivilege | Increase a process working set |
| SeInteractiveLogonRight | Allow log on locally |
| SeLoadDriverPrivilege | Load and unload device drivers |
| SeLockMemoryPrivilege | Lock pages in memory |
| SeMachineAccountPrivilege | Add workstations to domain |
| SeManageVolumePrivilege | Perform volume maintenance tasks |
| SeNetworkLogonRight | Access this computer from the network |
| SeProfileSingleProcessPrivilege | Profile single process |
| SeRelabelPrivilege | Modify an object label |
| SeRemoteInteractiveLogonRight | Allow log on through Remote Desktop Services |
| SeRemoteShutdownPrivilege | Force shutdown from a remote system |
| SeRestorePrivilege | Restore files and directories |
| SeSecurityPrivilege | Manage auditing and security log |
| SeServiceLogonRight | Log on as a service |
| SeShutdownPrivilege | Shut down the system |
| SeSyncAgentPrivilege | Synchronize directory service data |
| SeSystemEnvironmentPrivilege | Modify firmware environment values |
| SeSystemProfilePrivilege | Profile system performance |
| SeSystemtimePrivilege | Change the system time |
| SeTakeOwnershipPrivilege | Take ownership of files or other objects |
| SeTcbPrivilege | Act as part of the operating system |
| SeTimeZonePrivilege | Change the time zone |
| SeTrustedCredManAccessPrivilege | Access Credential Manager as a trusted caller |
| SeUndockPrivilege | Remove computer from docking station |
Note You may edit line 437 in the script to change what happens when the script is run without any arguments or parameters, this also allows you to change what happens when the script is run from the Powershell ISE.
Here are a few examples:
Add Users Single Users Example 1 Add User Right “Allow log on locally” for current user: . \Set-UserRights.ps1 -AddRight -UserRight SeInteractiveLogonRight Example 2 Add User Right “Log on as a service” for CONTOSO\User: . \Set-UserRights.ps1 -AddRight -Username CONTOSO\User -UserRight SeServiceLogonRight Example 3 Add User Right “Log on as a batch job” for CONTOSO\User: . \Set-UserRights.ps1 -AddRight -Username CONTOSO\User -UserRight SeBatchLogonRight Example 4 Add User Right “Log on as a batch job” for user SID S-1-5-11: . \Set-UserRights.ps1 -AddRight -Username S-1-5-11 -UserRight SeBatchLogonRight Add Multiple Users / Rights / Computers Example 5 Add User Right “Log on as a service” and “Log on as a batch job” for CONTOSO\User1 and CONTOSO\User2 and run on, local machine and SQL.contoso.com: . \Set-UserRights.ps1 -AddRight -UserRight SeServiceLogonRight , SeBatchLogonRight -ComputerName $ env : COMPUTERNAME , SQL.contoso.com -UserName CONTOSO\User1 , CONTOSO\User2
Remove Users Single Users Example 1 Remove User Right “Allow log on locally” for current user: . \Set-UserRights.ps1 -RemoveRight -UserRight SeInteractiveLogonRight Example 2 Remove User Right “Log on as a service” for CONTOSO\User: . \Set-UserRights.ps1 -RemoveRight -Username CONTOSO\User -UserRight SeServiceLogonRight Example 3 Remove User Right “Log on as a batch job” for CONTOSO\User: . \Set-UserRights.ps1 -RemoveRight -Username CONTOSO\User -UserRight SeBatchLogonRight Example 4 Remove User Right “Log on as a batch job” for user SID S-1-5-11: . \Set-UserRights.ps1 -RemoveRight -Username S-1-5-11 -UserRight SeBatchLogonRight Remove Multiple Users / Rights / Computers Example 5 Remove User Right “Log on as a service” and “Log on as a batch job” for CONTOSO\User1 and CONTOSO\User2 and run on, local machine and SQL.contoso.com: . \Set-UserRights.ps1 -RemoveRight -UserRight SeServiceLogonRight , SeBatchLogonRight -ComputerName $ env : COMPUTERNAME , SQL.contoso.com -UserName CONTOSO\User1 , CONTOSO\User2
Check User Rights
In order to check the Local User Rights, you will need to run the above (Get-UserRights), you may copy and paste the above script in your Powershell ISE and press play.
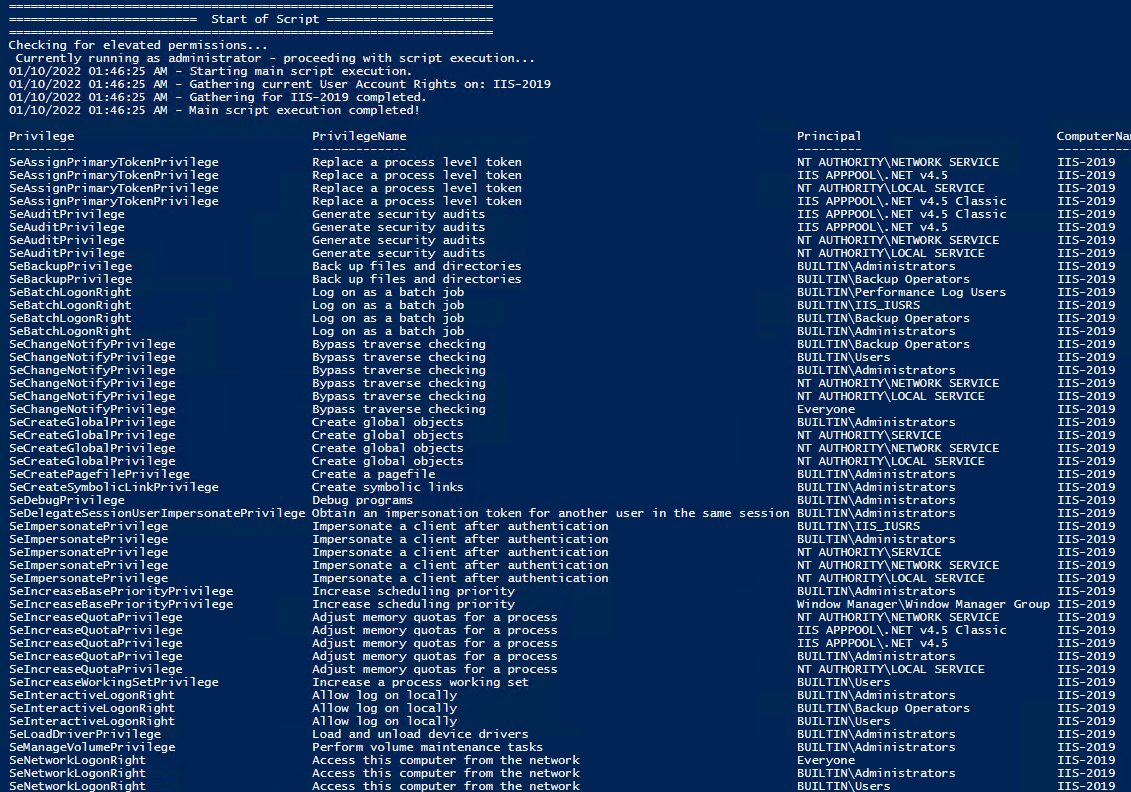
Note You may edit line 467 in the script to change what happens when the script is run without any arguments or parameters, this also allows you to change what happens when the script is run from the Powershell ISE.
Get Local User Account Rights and output to text in console:
Get Remote SQL Server User Account Rights:
Get Local Machine and SQL Server User Account Rights:
Output Local User Rights on Local Machine as CSV in ‘C:\Temp’:
Output to Text in ‘C:\Temp’:
PassThru object to allow manipulation / filtering:
I like to collaborate and work on projects. My skills with Powershell allow me to quickly develop automated solutions to suit my customers, and my own needs.
Email : [email protected]
Website : https://blakedrumm.com
My name is Blake Drumm, I am working on the Azure Monitoring Enterprise Team with Microsoft. Currently working to update public documentation for System Center products and write troubleshooting guides to assist with fixing issues that may arise while using the products. I like to blog on Operations Manager and Azure Automation products, keep checking back for new posts. My goal is to post atleast once a month if possible.
- operationsManager
- troubleshooting
- certificates

Windows security encyclopedia
#microsoft #windows #security
Search form
User rights assignment, related content.

Client, service, and program issues can occur if you change security settings and user rights assignments
Security settings and user rights assignments can be changed in local policies and group policies to help tighten the security on domain controllers and member computers. However, the downside of increased security is the introduction of incompatibilities with clients, services, and programs. This article describes incompatibilities that can occur on client computers that are running Windows XP, or an earlier version of Windows, when you change specific security settings and user rights assignments in a Windows Server 2003 domain or an earlier Windows Server domain. For information about Group Policy for Windows 7, Windows Server 2008 R2, and Windows Server 2008, see the following articles:
For Windows 7, see Group Policy management for IT pros
For Windows 7, and Windows Server 2008 R2, see What's New in Group Policy
Note: The remaining content in this article is specific to Windows XP, Windows Server 2003, and earlier versions of Windows.
To increase the awareness of misconfigured security settings, use the Group Policy Object Editor tool to change security settings. When you use Group Policy Object Editor, user rights assignments are enhanced on the following operating systems:
Windows XP Professional Service Pack 2 (SP2)
Windows Server 2003 Service Pack 1 (SP1)
The enhanced feature is a dialog box that contains a link to this article. The dialog box appears when you change a security setting or a user rights assignment to a setting that offers less compatibility and is more restrictive. If you directly change the same security setting or user rights assignment by using the registry or by using security templates, the effect is the same as changing the setting in Group Policy Object Editor. However, the dialog box that contains the link to this article does not appear. This article contains examples of clients, programs, and operations that are affected by specific security settings or user rights assignments. However, the examples are not authoritative for all Microsoft operating systems, for all third-party operating systems, or for all program versions that are affected. Not all security settings and user rights assignments are included in this article. We recommend that you validate the compatibility of all security-related configuration changes in a test forest before you introduce them in a production environment. The test forest must mirror the production forest in the following ways:
Client and server operating system versions, client and server programs, service pack versions, hotfixes, schema changes, security groups, group memberships, permissions on objects in the file system, shared folders, the registry, Active Directory directory service, local and Group Policy settings, and object count type and location
Administrative tasks that are performed, administrative tools that are used, and operating systems that are used to perform administrative tasks
Operations that are performed, such as the following:
Computer and user logon authentication
Password resets by users, by computers, and by administrators
Setting permissions for the file system, for shared folders, for the registry, and for Active Directory resources by using ACL Editor in all client operating systems in all account or resource domains from all client operating systems from all account or resource domains
Printing from administrative and nonadministrative accounts
Windows Server 2003 SP1
Warnings in gpedit.msc.
To help make customers aware that they are editing a user right or security option that could have adversely affect their network, two warning mechanisms were added to gpedit.msc. When administrators edit a user right that can adversely affect the whole enterprise, they will see a new icon that resembles a yield sign. They will also receive a warning message that has a link to Microsoft Knowledge Base article 823659. The text of this message is as follows:
Modifying this setting may affect compatibility with clients, services, and applications. For more information, see <user right or security option being modified> (Q823659) If you were directed to this Knowledge Base article from a link in Gpedit.msc, make sure that you read and understand the explanation provided and the possible effect of changing this setting. The following lists User Rights that contain the warning text:
Access this computer from network
Log on locally
Bypass traverse checking
Enable computers and users for trusted delegation
The following lists Security Options that have the warning and a pop-up message:
Domain Member: Digitally encrypt or sign secure channel data (always)
Domain Member: Require strong (Windows 2000 or a later version) session key
Domain Controller: LDAP server signing requirements
Microsoft network server: Digitally sign communications (always)
Network Access: Allows Anonymous Sid / Name translation
Network Access: Do not allow anonymous enumeration of SAM accounts and shares
Network security: LAN Manager Authentication level
Audit: Shut down system immediately if unable to log security audits
Network Access: LDAP client signing requirements
More Information
The following sections describe incompatibilities that can occur when you change specific settings in Windows NT 4.0 domains, Windows 2000 domains, and Windows Server 2003 domains.
User rights
The following list describes a user right, identifies configuration settings that may cause issues, describes why you should apply the user right and why you may want to remove the user right, and provides examples of compatibility issues that may occur when the user right is configured.
Background The ability to interact with remote Windows-based computers requires the Access this computer from network user right. Examples of such network operations include the following:
Replication of Active Directory between domain controllers in a common domain or forest
Authentication requests to domain controllers from users and from computers
Access to shared folders, printers, and other system services that are located on remote computers on the network
Users, computers, and service accounts gain or lose the Access this computer from network user right by being explicitly or implicitly added or removed from a security group that has been granted this user right. For example, a user account or a computer account may be explicitly added to a custom security group or a built-in security group by an administrator, or may be implicitly added by the operating system to a computed security group such as Domain Users, Authenticated Users, or Enterprise Domain Controllers. By default, user accounts and computer accounts are granted the Access this computer from network user right when computed groups such as Everyone or, preferably, Authenticated Users and, for domain controllers, the Enterprise Domain Controllers group, are defined in the default domain controllers Group Policy Object (GPO).
Risky configurations The following are harmful configuration settings:
Removing the Enterprise Domain Controllers security group from this user right
Removing the Authenticated Users group or an explicit group that allows users, computers, and service accounts the user right to connect to computers over the network
Removing all users and computers from this user right
Reasons to grant this user right
Granting the Access this computer from network user right to the Enterprise Domain Controllers group satisfies authentication requirements that Active Directory replication must have for replication to occur between domain controllers in the same forest.
This user right allows users and computers to access shared files, printers, and system services, including Active Directory.
This user right is required for users to access mail by using early versions of Microsoft Outlook Web Access (OWA).
Reasons to remove this user right
Users who can connect their computers to the network can access resources on remote computers that they have permissions for. For example, this user right is required for a user to connect to shared printers and to folders. If this user right is granted to the Everyone group, and if some shared folders have both share and NTFS file system permissions configured so that the same group has read access, anyone can view files in those shared folders. However, this is an unlikely situation for fresh installations of Windows Server 2003 because the default share and the NTFS permissions in Windows Server 2003 do not include the Everyone group. For systems that are upgraded from Microsoft Windows NT 4.0 or Windows 2000, this vulnerability may have a higher level of risk because the default share and the file system permissions for these operating systems are not as restrictive as the default permissions in Windows Server 2003.
There is no valid reason for removing Enterprise Domain Controllers group from this user right.
The Everyone group is generally removed in favor of the Authenticated Users group. If the Everyone group is removed, the Authenticated Users group must be granted this user right.
Windows NT 4.0 domains that are upgraded to Windows 2000 do not explicitly grant the Access this computer from network user right to the Everyone group, the Authenticated Users group, or the Enterprise Domain Controllers group. Therefore, when you remove the Everyone group from Windows NT 4.0 domain policy, Active Directory replication will fail with an "Access Denied" error message after you upgrade to Windows 2000. Winnt32.exe in Windows Server 2003 avoids this misconfiguration by granting the Enterprise Domain Controllers group this user right when you upgrade Windows NT 4.0 primary domain controllers (PDCs). Grant the Enterprise Domain Controllers group this user right if it is not present in the Group Policy Object Editor.
Examples of compatibility problems
Windows 2000 and Windows Server 2003: Replication of the following partitions will fail with "Access Denied" errors as reported by monitoring tools such as REPLMON and REPADMIN or replication events in the event log.
Active Directory Schema partition
Configuration partition
Domain partition
Global catalog partition
Application partition
All Microsoft network operating systems: User Account authentication from remote network client computers will fail unless the user or a security group that the user is a member of has been granted this user right.
All Microsoft network operating systems: Account authentication from remote network clients will fail unless the account or a security group the account is a member of has been granted this user right. This scenario applies to user accounts, to computer accounts, and to service accounts.
All Microsoft network operating systems: Removing all accounts from this user right will prevent any account from logging on to the domain or from accessing network resources. If computed groups such as Enterprise Domain Controllers, Everyone, or Authenticated Users are removed, you must explicitly grant this user right to accounts or to security groups that the account is a member of to access remote computers over the network. This scenario applies to all user accounts, to all computer accounts, and to all service accounts.
All Microsoft network operating systems: The local administrator account uses a "blank" password. Network connectivity with blank passwords is not permitted for administrator accounts in a domain environment. With this configuration, you can expect to receive an "Access Denied" error message.
Allow log on locally
Background Users who are trying to log on at the console of a Windows-based computer (by using the CTRL+ALT+DELETE keyboard shortcut) and accounts who are trying to start a service must have local logon privileges on the hosting computer. Examples of local logon operations include administrators who are logging on to the consoles of member computers, or domain controllers throughout the enterprise and domain users who are logging on to member computers to access their desktops by using non-privileged accounts. Users who use a Remote Desktop connection or Terminal Services must have the Allow log on locally user right on destination computers that are running Windows 2000 or Windows XP because these logon modes are considered local to the hosting computer. Users who are logging on to a server that has Terminal Server enabled and who do not have this user right can still start a remote interactive session in Windows Server 2003 domains if they have the Allow logon through Terminal Services user right.
Removing administrative security groups, including Account Operators, Backup Operators, Print Operators or Server Operators, and the built-in Administrators group from the default domain controller's policy.
Removing service accounts that are used by components and by programs on member computers and on domain controllers in the domain from the default domain controller's policy.
Removing users or security groups that log on to the console of member computers in the domain.
Removing service accounts that are defined in the local Security Accounts Manager (SAM) database of member computers or of workgroup computers.
Removing non-built-in administrative accounts that are authenticating over Terminal Services that is running on a domain controller.
Adding all user accounts in the domain explicitly or implicitly through the Everyone group to the Deny logon locally logon right. This configuration will prevent users from logging on to any member computer or to any domain controller in the domain.
Users must have the Allow log on locally user right to access the console or the desktop of a workgroup computer, a member computer, or a domain controller.
Users must have this user right to log on over a Terminal Services session that is running on a Window 2000-based member computer or domain controller.
Failure to restrict console access to legitimate user accounts could result in unauthorized users downloading and executing malicious code to change their user rights.
Removal of the Allow log on locally user right prevents unauthorized logons on the consoles of computers, such as domain controllers or application servers.
Removal of this logon right prevents non-domain accounts from logging on at the console of member computers in the domain.
Windows 2000 terminal servers: The Allow log on locally user right is required for users to log on to Windows 2000 terminal servers.
Windows NT 4.0, Windows 2000, Windows XP, or Windows Server 2003: User accounts must be granted this user right to log on at the console of computers that are running Windows NT 4.0, Windows 2000, Windows XP, or Windows Server 2003.
Windows NT 4.0 and later: On computers that are running Windows NT 4.0 and later, if you add the Allow log on locally user right, but you implicitly or explicitly also grant the Deny logon locally logon right, the accounts will not be able to log on to the console of the domain controllers.
Background The Bypass traverse checking user right allows the user to browse through folders in the NTFS file system or in the registry without checking for the Traverse Folder special access permission. The Bypass traverse checking user right does not allow the user to list the contents of a folder. It allows the user to traverse only its folders.
Removing non-administrative accounts that log on to Windows 2000-based Terminal Services computers or Windows Server 2003-based Terminal Services computers that do not have permissions to access files and folders in the file system.
Removing the Everyone group from the list of security principals who have this user right by default. Windows operating systems, and also many programs, are designed with the expectation that anyone who can legitimately access the computer will have the Bypass traverse checking user right. Therefore, removing the Everyone group from the list of security principals who have this user right by default could lead to operating system instability or to program failure. It is better that you leave this setting at its default.
Reasons to grant this user right The default setting for the Bypass traverse checking user right is to allow anyone to bypass traverse checking. For experienced Windows system administrators, this is the expected behavior, and they configure file system access control lists (SACLs) accordingly. The only scenario where the default configuration may lead to a mishap is if the administrator who configures permissions does not understand the behavior and expects that users who cannot access a parent folder will not be able to access the contents of any child folders.
Reasons to remove this user right To try to prevent access to the files or the folders in the file system, organizations that are very concerned about security may be tempted to remove the Everyone group, or even the Users group, from the list of groups that have the Bypass traverse checking user right.
Windows 2000, Windows Server 2003: If the Bypass traverse checking user right is removed or is misconfigured on computers that are running Windows 2000 or Windows Server 2003, Group Policy settings in the SYVOL folder will not replicate between domain controllers in the domain.
Windows 2000, Windows XP Professional, Windows Server 2003: Computers that are running Windows 2000, Windows XP Professional, or Windows Server 2003 will log events 1000 and 1202 and will not be able to apply computer policy and user policy when the required file system permissions are removed from the SYSVOL tree if the Bypass traverse checking user right is removed or is misconfigured.
Windows 2000, Windows Server 2003: On computers that are running Windows 2000 or Windows Server 2003, the Quota tab in Windows Explorer will disappear when you view properties on a volume.
Windows 2000: Non-administrators who log on to a Windows 2000 terminal server may receive the following error message:
Userinit.exe application error. The application failed to initialize properly 0xc0000142 click OK to terminate the app.
Windows NT 4.0, Windows 2000, Windows XP, Windows Server 2003: Users whose computers are running Windows NT 4.0, Windows 2000, Windows XP, or Windows Server 2003 may not be able to access shared folders or files on shared folders, and they may receive "Access Denied" error messages if they are not granted the Bypass traverse checking user right.
Windows NT 4.0: On Windows NT 4.0-based computers, removal of the Bypass traverse checking user right will cause a file copy to drop file streams. If you remove this user right, when a file is copied from a Windows client or from a Macintosh client to a Windows NT 4.0 domain controller that is running Services for Macintosh, the destination file stream is lost, and the file appears as a text-only file.
Microsoft Windows 95, Microsoft Windows 98: On a client computer that is running Windows 95 or Windows 98, the net use * /home command will fail with an "Access Denied" error message if the Authenticated Users group is not granted the Bypass traverse checking user right.
Outlook Web Access: Non-administrators will not be able to log on to Microsoft Outlook Web Access, and they will receive an "Access Denied" error message if they are not granted the Bypass traverse checking user right.
Security Settings
The following list identifies a security setting, and the nested list provides a description about the security setting, identifies configuration settings that may cause issues, describes why you should apply the security setting, and then describes reasons why you may want to remove the security setting. The nested list then provides a symbolic name for the security setting and the registry path of the security setting. Finally, examples are provided of compatibility issues that may occur when the security setting is configured.
The Audit: Shut down system immediately if unable to log security audits setting determines whether the system shuts down if you cannot log security events. This setting is required for the Trusted Computer Security Evaluation Criteria (TCSEC) program's C2 evaluation and for the Common Criteria for Information Technology Security Evaluation to prevent auditable events if the audit system can't log those events. If the auditing system fails, the system is shut down, and a Stop error message appears.
If the computer cannot record events to the security log, critical evidence or important troubleshooting information may not be available for review after a security incident.
Risky configuration The following is a harmful configuration setting: The Audit: Shut down system immediately if unable to log security audits setting is turned on, and the size of the security event log is constrained by the Do not overwrite events (clear log manually) option, the Overwrite Events as needed option, or the Overwrite Events older than number days option in Event Viewer. See the "Examples of Compatibility Problems" section for information about specific risks for computers that are running the original released version of Windows 2000, Windows 2000 Service Pack 1 (SP1), Windows 2000 SP2, or Windows 2000 SP3.
Reasons to enable this setting If the computer cannot record events to the security log, critical evidence or important troubleshooting information may not be available for review after a security incident.
Reasons to disable this setting
Enabling the Audit: Shut down system immediately if unable to log security audits setting stops the system if a security audit cannot be logged for any reason. Typically, an event cannot be logged when the security audit log is full and when its specified retention method is either the Do not overwrite events (clear log manually) option or the Overwrite Events older than number days option.
The administrative burden of enabling the Audit: Shut down system immediately if unable to log security audits setting can be very high, especially if you also turn on the Do not overwrite events (clear log manually) option for the security log. This setting provides for individual accountability of operator actions. For example, an administrator could reset permissions on all users, computers, and groups in an organizational unit (OU) where auditing was enabled by using the built-in administrator account or other shared account and then deny that they reset such permissions. However, enabling the setting does reduce the robustness of the system because a server may be forced to shut down by overwhelming it with logon events and with other security events that are written to the security log. Additionally, because the shutdown is not graceful, irreparable damage to the operating system, programs, or data may result. While NTFS guarantees that the file system’s integrity is maintained during an ungraceful system shutdown, it cannot guarantee that every data file for every program will still be in a usable form when the system restarts.
Symbolic Name: CrashOnAuditFail
Registry Path:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\CrashOnAuditFail (Reg_DWORD)
Windows 2000: Because of a bug, computers that are running the original released version of Windows 2000, Windows 2000 SP1, Windows 2000 SP2, or Windows Server SP3 may stop logging events before the size that is specified in the Maximum log size option for the security event log is reached. This bug is fixed in Windows 2000 Service Pack 4 (SP4). Make sure that your Windows 2000 domain controllers have Windows 2000 Service Pack 4 installed before you consider enabling this setting.
Windows 2000, Windows Server 2003: Computers that are running Windows 2000 or Windows Server 2003 may stop responding and then may spontaneously restart if the Audit: Shut down system immediately if unable to log security audits setting is turned on, the security log is full, and an existing event log entry cannot be overwritten. When the computer restarts, the following Stop error message appears:
STOP: C0000244 {Audit Failed} An attempt to generate a security audit failed.
To recover, an administrator must log on, archive the security log (optional), clear the security log, and then reset this option (optional and as-needed).
Microsoft Network Client for MS-DOS, Windows 95, Windows 98, Windows NT 4.0, Windows 2000, Windows XP, Windows Server 2003: Non-administrators who try to log on to a domain will receive the following error message:
Your account is configured to prevent you from using this computer. Please try another computer.
Windows 2000: On Windows 2000-based computers, non-administrators will not be able to log on to remote access servers, and they will receive an error message that is similar to the following:
Unknown user or bad password
Windows 2000: On Windows 2000 domain controllers, the Intersite Messaging service (Ismserv.exe) will stop and cannot be restarted. DCDIAG will report the error as "failed test services ISMserv," and event ID 1083 will be registered in the event log.
Windows 2000: On Windows 2000 domain controllers, Active Directory replication will fail, and an "Access Denied" message will appear if the security event log is full.
Microsoft Exchange 2000: Servers that are running Exchange 2000 will not be able to mount the information store database, and event 2102 will be registered in the event log.
Outlook, Outlook Web Access: Non-administrators will not be able to access their mail through Microsoft Outlook or through Microsoft Outlook Web Access, and they will receive a 503 error.
Domain controller: LDAP server signing requirements
Background The Domain controller: LDAP server signing requirements security setting determines whether the Lightweight Directory Access Protocol (LDAP) server requires LDAP clients to negotiate data signing. The possible values for this policy setting are as follows:
None: Data signing is not required to bind with the server. If the client requests data signing, the server supports it.
Require signing: The LDAP data-signing option must be negotiated unless Transport Layer Security/Secure Socket Layer (TLS/SSL) is being used.
not defined: This setting is not enabled or disabled.
Enabling Require signing in environments where clients do not support LDAP signing or where client-side LDAP signing is not enabled on the client
Applying the Windows 2000 or the Windows Server 2003 Hisecdc.inf security template in environments where the clients do not support LDAP signing or where client-side LDAP signing is not enabled
Applying the Windows 2000 or the Windows Server 2003 Hisecws.inf security template in environments where the clients do not support LDAP signing or where client-side LDAP signing is not enabled
Reasons to enable this setting Unsigned network traffic is susceptible to man-in-the-middle attacks where an intruder captures packets between the client and the server, modifies the packets, and then forwards them to the server. When this behavior occurs on an LDAP server, an attacker could cause a server to make decisions that are based on false queries from the LDAP client. You can lower this risk in a corporate network by implementing strong physical security measures to help protect the network infrastructure. Internet Protocol security (IPSec) authentication header mode can help prevent man-in-the-middle attacks. Authentication header mode performs mutual authentication and packet integrity for IP traffic.
Clients that do not support LDAP signing will not be able to carry out LDAP queries against domain controllers and against global catalogs if NTLM authentication is negotiated and if the correct service packs are not installed on Windows 2000 domain controllers.
Network traces of LDAP traffic between clients and servers will be encrypted. This makes it difficult to examine LDAP conversations.
Windows 2000-based servers must have Windows 2000 Service Pack 3 (SP3) or installed when they are administered with programs that support LDAP signing that are run from client computers that run Windows 2000 SP4, Windows XP, or Windows Server 2003.
Symbolic Name: LDAPServerIntegrity
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\NTDS\Parameters\LDAPServerIntegrity (Reg_DWORD)
Simple binds will fail, and you will receive the following error message:
Ldap_simple_bind_s() failed: Strong Authentication Required.
Windows 2000 Service Pack 4, Windows XP, Windows Server 2003: On clients that are running Windows 2000 SP4, Windows XP, or Windows Server 2003, some Active Directory administration tools will not operate correctly against domain controllers that are running versions of Windows 2000 that are earlier than SP3 when NTLM authentication is negotiated.
Windows 2000 Service Pack 4, Windows XP, Windows Server 2003: On clients that are running Windows 2000 SP4, Windows XP, or Windows Server 2003, some Active Directory administration tools that target domain controllers that are running versions of Windows 2000 that are earlier than SP3 will not operate correctly if they are using IP addresses (for example, "dsa.msc /server= x.x.x.x " where x.x.x.x is an IP address).
Windows 2000 Service Pack 4, Windows XP, Windows Server 2003: On clients that are running Windows 2000 SP4, Windows XP, or Windows Server 2003, some Active Directory administration tools that target domain controllers that are running versions of Windows 2000 that are earlier than SP3 will not operate correctly.
Domain member: Require strong (Windows 2000 or later) session key
The Domain member: Require strong (Windows 2000 or later) session key setting determines whether a secure channel can be established with a domain controller that cannot encrypt secure channel traffic with a strong, 128-bit session key. Enabling this setting prevents establishing a secure channel with any domain controller that cannot encrypt secure channel data with a strong key. Disabling this setting allows 64-bit session keys.
Before you can enable this setting on a member workstation or on a server, all domain controllers in the domain that the member belongs to must be able to encrypt secure channel data with a strong, 128-bit key. This means that all such domain controllers must be running Windows 2000 or later.
Risky configuration Enabling the Domain member: Require strong (Windows 2000 or later) session key setting is a harmful configuration setting.
Reasons to enable this setting
Session keys that are used to establish secure channel communications between member computers and domain controllers are much stronger in Windows 2000 than they are in earlier versions of Microsoft operating systems.
When it's possible, it is a good idea to take advantage of these stronger session keys to help protect secure channel communications from eavesdropping and from session hijacking network attacks. Eavesdropping is a form of malicious attack where network data is read or is altered in transit. The data can be modified to hide or to change the sender, or to redirect it.
Important A computer that is running Windows Server 2008 R2 or Windows 7 supports only strong keys when secure channels are used. This restriction prevents a trust between any Windows NT 4.0-based domain and any Windows Server 2008 R2-based domain. Additionally, this restriction blocks the Windows NT 4.0-based domain membership of computers that are running Windows 7 or Windows Server 2008 R2, and vice versa.
Reasons to disable this setting The domain contains member computers that are running operating systems other than Windows 2000, Windows XP, or Windows Server 2003.
Symbolic Name: StrongKey
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Netlogon\Parameters\RequireStrongKey (Reg_DWORD)
Examples of compatibility problems Windows NT 4.0: On Windows NT 4.0-based computers, resetting secure channels of trust relationships between Windows NT 4.0 and Windows 2000 domains with NLTEST fails. An "Access Denied" error message appears:
The trust relationship between the primary domain and the trusted domain failed. Windows 7 and Server 2008 R2: For Windows 7 and later versions and Windows Server 2008 R2 and later versions, this setting is not honored any longer and the strong key is used always. Because of that, trusts with Windows NT 4.0 domains do not work any longer.
Domain member: Digitally encrypt or sign secure channel data (always)
Enabling Domain member: Digitally encrypt or sign secure channel data (always) prevents establishing a secure channel with any domain controller that cannot sign or encrypt all secure channel data. To help protect authentication traffic from man-in-the-middle attacks, replay attacks, and other kinds of network attacks, Windows-based computers create a communication channel that is known as a secure channel through the Net Logon service to authenticate computer accounts. Secure channels are also used when a user in one domain connects to a network resource in a remote domain. This multidomain authentication, or pass-through authentication, allows a Windows-based computer that has joined a domain to have access to the user account database in its domain and in any trusted domains.
To enable the Domain member: Digitally encrypt or sign secure channel data (always) setting on a member computer, all domain controllers in the domain that the member belongs to must be able to sign or encrypt all secure channel data. This means that all such domain controllers must be running Windows NT 4.0 with Service Pack 6a (SP6a) or later.
Enabling the Domain member: Digitally encrypt or sign secure channel data (always) setting automatically enables the Domain member: Digitally encrypt or sign secure channel data (when possible) setting.
Risky configuration Enabling the Domain member: Digitally encrypt or sign secure channel data (always) setting in domains where not all domain controllers can sign or encrypt secure channel data is a harmful configuration setting.
Reasons to enable this setting Unsigned network traffic is susceptible to man-in-the-middle attacks, where an intruder captures packets between the server and the client and then modifies them before forwarding them to the client. When this behavior occurs on an Lightweight Directory Access Protocol (LDAP) server, the intruder could cause a client to make decisions that are based on false records from the LDAP directory. You can lower the risk of such an attack on a corporate network by implementing strong physical security measures to help protect the network infrastructure. Additionally, implementing Internet Protocol security (IPSec) authentication header mode can help prevent man-in-the-middle attacks. This mode performs mutual authentication and packet integrity for IP traffic.
Computers in local or external domains do support encrypted secure channels.
Not all domain controllers in the domain have the appropriate service pack revision levels to support encrypted secure channels.
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Netlogon\Parameters\RequireSignOrSeal (REG_DWORD)
Windows NT 4.0: Windows 2000-based member computers will not be able to join Windows NT 4.0 domains and will receive the following error message:
The account is not authorized to log in from this station.
For more information, click the following article number to view the article in the Microsoft Knowledge Base:
281648 Error message: The account is not authorized to login from this station
Windows NT 4.0: Windows NT 4.0 domains will not be able to establish a down-level trust with a Windows 2000 domain and will receive the following error message:
Existing down-level trusts may also not authenticate users from the trusted domain. Some users may have problems logging on to the domain, and they may receive an error message that states that the client cannot find the domain.
Windows XP: Windows XP clients that are joined to Windows NT 4.0 domains will not be able to authenticate logon attempts and may receive the following error message, or the following events may be registered in the event log:
Windows cannot connect to the domain either because the domain controller is down or is otherwise unavailable or because your computer account was not found
Microsoft Network: Microsoft Network clients will receive one of the following error messages:
Logon failure: unknown username or bad password.
There is no user session key for the specified logon session.
Microsoft network client: Digitally sign communications (always)
Background Server Message Block (SMB) is the resource-sharing protocol that is supported by many Microsoft operating systems. It is the basis of network basic input/output system (NetBIOS) and of many other protocols. SMB signing authenticates both the user and the server that hosts the data. If either side fails the authentication process, data transmission will not occur. Enabling SMB signing starts during SMB protocol negotiation. The SMB signing policies determine whether the computer always digitally signs client communications. The Windows 2000 SMB authentication protocol supports mutual authentication. Mutual authentication closes a "man-in-the-middle" attack. The Windows 2000 SMB authentication protocol also supports message authentication. Message authentication helps prevent active message attacks. To give you this authentication, SMB signing puts a digital signature into each SMB. The client and the server each verify the digital signature. To use SMB signing, you must enable SMB signing or require SMB signing on both the SMB client and the SMB server. If SMB signing is enabled on a server, clients that are also enabled for SMB signing use the packet signing protocol during all subsequent sessions. If SMB signing is required on a server, a client cannot establish a session unless the client is enabled or required for SMB signing. Enabling digital signing in high-security networks helps prevent the impersonation of clients and of servers. This kind of impersonation is known as session hijacking. An attacker who has access to the same network as the client or the server uses session hijacking tools to interrupt, end, or steal a session in progress. An attacker could intercept and modify unsigned SMB packets, modify the traffic, and then forward it so that the server might perform unwanted actions. Or, the attacker could pose as the server or as the client after a legitimate authentication and then gain unauthorized access to data. The SMB protocol that is used for file sharing and for print sharing in computers that are running Windows 2000 Server, Windows 2000 Professional, Windows XP Professional, or Windows Server 2003 supports mutual authentication. Mutual authentication closes session hijacking attacks and supports message authentication. Therefore, it prevents man-in-the-middle attacks. SMB signing provides this authentication by placing a digital signature in each SMB. The client and the server then verify the signature. Notes
As an alternative countermeasure, you can enable digital signatures with IPSec to help protect all network traffic. There are hardware-based accelerators for IPSec encryption and signing that you can use to minimize the performance impact from the server's CPU. There are no such accelerators that are available for SMB signing. For more information, see the Digitally sign server communications chapter on the Microsoft MSDN website. Configure SMB signing through Group Policy Object Editor because a change to a local registry value has no effect if there is an overriding domain policy.
In Windows 95, Windows 98, and Windows 98 Second Edition, the Directory Services Client uses SMB signing when it authenticates with Windows Server 2003 servers by using NTLM authentication. However, these clients do not use SMB signing when they authenticate with these servers by using NTLMv2 authentication. Additionally, Windows 2000 servers do not respond to SMB signing requests from these clients. For more information, see item 10: "Network security: Lan Manager authentication level."
Risky configuration The following is a harmful configuration setting: Leaving both the Microsoft network client: Digitally sign communications (always) setting and the Microsoft network client: Digitally sign communications (if server agrees) setting set to "Not Defined" or disabled. These settings allow the redirector to send plain text passwords to non-Microsoft SMB servers that do not support password encryption during authentication.
Reasons to enable this setting Enabling Microsoft network client: Digitally sign communications (always) requires clients to sign SMB traffic when contacting servers that do not require SMB signing. This makes clients less vulnerable to session hijacking attacks.
Enabling Microsoft network client: Digitally sign communications (always) prevents clients from communicating with target servers that do not support SMB signing.
Configuring computers to ignore all unsigned SMB communications prevents earlier programs and operating systems from connecting.
Symbolic Name: RequireSMBSignRdr
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanWorkstation\Parameters\RequireSecuritySignature
Windows NT 4.0: You will not be able to reset the secure channel of a trust between a Windows Server 2003 domain and a Windows NT 4.0 domain by using NLTEST or NETDOM, and you will receive an "Access Denied" error message.
Windows XP: Copying files from Windows XP clients to Windows 2000-based servers and to Windows Server 2003-based servers may take more time.
You will not be able to map a network drive from a client with this setting enabled, and you will receive the following error message:
Restart requirements Restart the computer, or restart the Workstation service. To do this, type the following commands at a command prompt. Press Enter after you type each command.
net stop workstation net start workstation
Server Messenger Block (SMB) is the resource-sharing protocol that is supported by many Microsoft operating systems. It is the basis of network basic input/output system (NetBIOS) and of many other protocols. SMB signing authenticates both the user and the server that hosts the data. If either side fails the authentication process, data transmission will not occur. Enabling SMB signing starts during SMB protocol negotiation. The SMB signing policies determine whether the computer always digitally signs client communications. The Windows 2000 SMB authentication protocol supports mutual authentication. Mutual authentication closes a "man-in-the-middle" attack. The Windows 2000 SMB authentication protocol also supports message authentication. Message authentication helps prevent active message attacks. To give you this authentication, SMB signing puts a digital signature into each SMB. The client and the server each verify the digital signature. To use SMB signing, you must enable SMB signing or require SMB signing on both the SMB client and the SMB server. If SMB signing is enabled on a server, clients that are also enabled for SMB signing use the packet signing protocol during all subsequent sessions. If SMB signing is required on a server, a client cannot establish a session unless the client is enabled or required for SMB signing. Enabling digital signing in high-security networks helps prevent the impersonation of clients and of servers. This kind of impersonation is known as session hijacking. An attacker who has access to the same network as the client or the server uses session hijacking tools to interrupt, end, or steal a session in progress. An attacker could intercept and modify unsigned Subnet Bandwidth Manager (SBM) packets, modify the traffic, and then forward it so that the server might perform unwanted actions. Or, the attacker could pose as the server or as the client after a legitimate authentication and then gain unauthorized access to data. The SMB protocol that is used for file sharing and for print sharing in computers that are running Windows 2000 Server, Windows 2000 Professional, Windows XP Professional, or Windows Server 2003 supports mutual authentication. Mutual authentication closes session hijacking attacks and supports message authentication. Therefore, it prevents man-in-the-middle attacks. SMB signing provides this authentication by placing a digital signature in each SMB. The client and the server then verify the signature.
As an alternative countermeasure, you can enable digital signatures with IPSec to help protect all network traffic. There are hardware-based accelerators for IPSec encryption and signing that you can use to minimize the performance impact from the server's CPU. There are no such accelerators that are available for SMB signing.
Risky configuration The following is a harmful configuration setting: Enabling the Microsoft network server: Digitally sign communications (always) setting on servers and on domain controllers that are accessed by incompatible Windows-based computers and third-party operating system-based client computers in local or external domains.
All client computers that enable this setting directly through the registry or through the Group Policy setting support SMB signing. In other words, all client computers that have this setting enabled run either Windows 95 with the DS client installed, Windows 98, Windows NT 4.0, Windows 2000, Windows XP Professional, or Windows Server 2003.
If Microsoft network server: Digitally sign communications (always) is disabled, SMB signing is completely disabled. Completely disabling all SMB signing leaves computers more vulnerable to session hijacking attacks.
Enabling this setting may cause slower file copy and network performance on client computers.
Enabling this setting will prevent clients that cannot negotiate SMB signing from communicating with servers and with domain controllers. This causes operations such as domain joins, user and computer authentication, or network access by programs to fail.
Symbolic Name: RequireSMBSignServer
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanManServer\Parameters\RequireSecuritySignature (REG_DWORD)
Windows 95: Windows 95 clients that do not have the Directory Services (DS) Client installed will fail logon authentication and will receive the following error message:
The domain password you supplied is not correct, or access to your logon server has been denied.
Windows NT 4.0: Client computers that are running versions of Windows NT 4.0 that are earlier than Service Pack 3 (SP3) will fail logon authentication and will receive the following error message:
The system could not log you on. Make sure your username and your domain are correct, then type your password again.
Some non-Microsoft SMB servers support only unencrypted password exchanges during authentication. (These exchanges also known as "plain text" exchanges.) For Windows NT 4.0 SP3 and later versions, the SMB redirector does not send an unencrypted password during authentication to an SMB server unless you add a specific registry entry. To enable unencrypted passwords for the SMB client on Windows NT 4.0 SP 3 and newer systems, modify the registry as follows: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Rdr\Parameters Value Name: EnablePlainTextPassword Data Type: REG_DWORD Data: 1
Windows Server 2003: By default, security settings on domain controllers that run Windows Server 2003 are configured to help prevent domain controller communications from being intercepted or tampered with by malicious users. For users to successfully communicate with a domain controller that runs Windows Server 2003, client computers must use both SMB signing and encryption or secure channel traffic signing. By default, clients that run Windows NT 4.0 with Service Pack 2 (SP2) or earlier installed and clients that run Windows 95 do not have SMB packet signing enabled. Therefore, these clients may not be able to authenticate to a Windows Server 2003-based domain controller.
Windows 2000 and Windows Server 2003 policy settings: Depending on your specific installation needs and configuration, we recommend that you set the following policy settings at the lowest entity of necessary scope in the Microsoft Management Console Group Policy Editor snap-in hierarchy:
Computer Configuration\Windows Security Settings\Security Options
Send unencrypted password to connect to third-party SMB servers (this setting is for Windows 2000)
Microsoft network client: Send unencrypted password to third-party SMB servers (this setting is for Windows Server 2003)
Note In some third-party CIFS servers, such as older Samba versions, you cannot use encrypted passwords.
The following clients are incompatible with the Microsoft network server: Digitally sign communications (always) setting:
Apple Computer, Inc., Mac OS X clients
Microsoft MS-DOS network clients (for example, Microsoft LAN Manager)
Microsoft Windows for Workgroups clients
Microsoft Windows 95 clients without the DS Client installed
Microsoft Windows NT 4.0-based computers without SP3 or later installed
Novell Netware 6 CIFS clients
SAMBA SMB clients that do not have support for SMB signing
Restart requirements Restart the computer, or restart the Server service. To do this, type the following commands at a command prompt. Press Enter after you type each command.
net stop server net start server
Network access: Allow anonymous SID/Name translation
Background The Network access: Allow anonymous SID/Name translation security setting determines whether an anonymous user can request Security Identification Number (SID) attributes for another user.
Risky configuration Enabling the Network access: Allow anonymous SID/Name translation setting is a harmful configuration setting.
Reasons to enable this setting If the Network access: Allow anonymous SID/Name translation setting is disabled, earlier operating systems or applications may not be able to communicate with Windows Server 2003 domains. For example, the following operating systems, services, or applications may not work:
Windows NT 4.0-based Remote Access Service servers
Microsoft SQL Server that are running on Windows NT 3.x-based computers or Windows NT 4.0-based computers
Remote Access Service that is running on Windows 2000-based computers that are located in Windows NT 3.x domains or Windows NT 4.0 domains
SQL Server that is running on Windows 2000-based computers that are located in Windows NT 3.x domains or in Windows NT 4.0 domains
Users in Windows NT 4.0 resource domain who want to grant permissions to access files, shared folders, and registry objects to user accounts from account domains that contain Windows Server 2003 domain controllers
Reasons to disable this setting If this setting is enabled, a malicious user could use the well-known Administrators SID to obtain the real name of the built-in Administrator account, even if the account has been renamed. That person could then use the account name to initiate a password-guessing attack.
Symbolic Name: N/A
Registry Path: None. The path is specified in UI code.
Examples of compatibility problems Windows NT 4.0: Computers in Windows NT 4.0 resource domains will display the "Account Unknown" error message in ACL Editor if resources, including shared folders, shared files, and registry objects, are secured with security principals that reside in account domains that contain Windows Server 2003 domain controllers.
Network access: Do not allow anonymous enumeration of SAM accounts
The Network access: Do not allow anonymous enumeration of SAM accounts setting determines which additional permissions will be granted for anonymous connections to the computer. Windows allows anonymous users to perform certain activities, such as enumerating the names of workstation and server Security Accounts Manager (SAM) accounts and of network shares. For example, an administrator can use this to grant access to users in a trusted domain that does not maintain a reciprocal trust. Once a session is made, an anonymous user may have the same access that is granted to the Everyone group based on the setting in the Network access: Let Everyone permissions apply to anonymous users setting or the discretionary access control list (DACL) of the object. Typically, anonymous connections are requested by earlier versions of clients (down-level clients) during SMB session setup. In these cases, a network trace shows that the SMB Process ID (PID) is the client redirector such as 0xFEFF in Windows 2000 or 0xCAFE in Windows NT. RPC may also try to make anonymous connections.
Important This setting has no impact on domain controllers. On domain controllers, this behavior is controlled by the presence of "NT AUTHORITY\ANONYMOUS LOGON" in "Pre-Windows 2000 compatible Access".
In Windows 2000, a similar setting called Additional Restrictions for Anonymous Connections manages the RestrictAnonymous registry value. The location of this value is as follows
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA
Risky configurations Enabling the Network access: Do not allow anonymous enumeration of SAM accounts setting is a harmful configuration setting from a compatibility perspective. Disabling it is a harmful configuration setting from a security perspective.
Reasons to enable this setting An unauthorized user could anonymously list account names and then use the information to try to guess passwords or to perform social engineering attacks. Social engineering is jargon that means tricking people into revealing their passwords or some form of security information.
Reasons to disable this setting If this setting is enabled, it is impossible to establish trusts with Windows NT 4.0 domains. This setting also causes problems with down-level clients (such as Windows NT 3.51 clients and Windows 95 clients) that are trying to use resources on the server.
Symbolic Name: RestrictAnonymousSAM
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\RestrictAnonymousSAM (Reg_DWORD)
SMS Network Discovery will not be able to obtain operating system information and will write "Unknown" in the OperatingSystemNameandVersion property.
Windows 95, Windows 98: Windows 95 clients and Windows 98 clients will not be able to change their passwords.
Windows NT 4.0: Windows NT 4.0-based member computers will not be able to be authenticated.
Windows 95, Windows 98: Windows 95-based and Windows 98-based computers will not be able to be authenticated by Microsoft domain controllers.
Windows 95, Windows 98: Users on Windows 95-based and Windows 98-based computers will not be able to change the passwords for their user accounts.
Network access: Do not allow anonymous enumeration of SAM accounts and shares
The Network access: Do not allow anonymous enumeration of SAM accounts and shares setting (also known as RestrictAnonymous) determines whether anonymous enumeration of Security Accounts Manager (SAM) accounts and shares is allowed. Windows allows anonymous users to perform certain activities, such as enumerating the names of domain accounts (users, computers, and groups) and of network shares. This is convenient, for example, when an administrator wants to grant access to users in a trusted domain that does not maintain a reciprocal trust. If you do not want to allow anonymous enumeration of SAM accounts and of shares, enable this setting.
In Windows 2000, a similar setting called Additional Restrictions for Anonymous Connections manages the RestrictAnonymous registry value. The location of this value is as follows:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA
Risky configuration Enabling the Network access: Do not allow anonymous enumeration of SAM accounts and shares setting is a harmful configuration setting.
Enabling the Network access: Do not allow anonymous enumeration of SAM accounts and shares setting prevents enumeration of SAM accounts and shares by users and computers that are using anonymous accounts.
If this setting is enabled, an unauthorized user could anonymously list account names and then use the information to try to guess passwords or to perform social engineering attacks. Social engineering is jargon that means tricking people into revealing their password or some form of security information.
If this setting is enabled, it will be impossible to establish trusts with Windows NT 4.0 domains. This setting will also cause problems with down-level clients such as Windows NT 3.51 and Windows 95 clients that are trying to use resources on the server.
It will be impossible to grant access to users of resource domains because administrators in the trusting domain will not be able to enumerate lists of accounts in the other domain. Users who access file and print servers anonymously will not be able to list the shared network resources on those servers. The users must authenticate before they can view the lists of shared folders and printers.
Symbolic Name: RestrictAnonymous
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\RestrictAnonymous
Windows NT 4.0: Users will not be able to change their passwords from Windows NT 4.0 workstations when RestrictAnonymous is enabled on domain controllers in the users' domain.
Windows NT 4.0: Adding users or global groups from trusted Windows 2000 domains to Windows NT 4.0 local groups in User Manager will fail, and the following error message will appear:
There are currently no logon servers available to service the logon request.
Windows NT 4.0: Windows NT 4.0-based computers will not be able to join domains during setup or by using the domain join user interface.
Windows NT 4.0: Establishing a down-level trust with Windows NT 4.0 resource domains will fail. The following error message will appear when RestrictAnonymous is enabled on the trusted domain:
Could not find domain controller for this domain.
Windows NT 4.0: Users who log on to Windows NT 4.0-based Terminal Server computers will map to the default home directory instead of the home directory that is defined in User Manager for domains.
Windows NT 4.0: Windows NT 4.0 backup domain controllers (BDCs) will not be able to start the Net Logon service, obtain a list of backup browsers, or synchronize the SAM database from Windows 2000 or from Windows Server 2003 domain controllers in the same domain.
Windows 2000: Windows 2000-based member computers in Windows NT 4.0 domains will not be able to view printers in external domains if the No access without explicitly anonymous permissions setting is enabled in the local security policy of the client computer.
Windows 2000: Windows 2000 domain users will not be able to add network printers from Active Directory; however, they will be able to add printers after they select them from the tree view.
Windows 2000: On Windows 2000-based computers, ACL Editor will not be able to add users or global groups from trusted Windows NT 4.0 domains.
ADMT version 2: Password migration for user accounts that are migrated between forests with Active Directory Migration Tool (ADMT) version 2 will fail. For more information, click the following article number to view the article in the Microsoft Knowledge Base:
322981 How to troubleshoot inter-forest password migration with ADMTv2
Outlook clients: The global address list will appear empty to Microsoft Exchange Outlook clients.
SMS: Microsoft Systems Management Server (SMS) Network Discovery will not be able to obtain the operating system information. Therefore, it will write "Unknown" in the OperatingSystemNameandVersion property of the SMS DDR property of the discovery data record (DDR).
SMS: When you use the SMS Administrator User Wizard to browse for users and groups, no users or groups will be listed. Additionally, Advanced clients cannot communicate with the Management Point. Anonymous access is required on the Management Point.
SMS: When you are using the Network Discovery feature in SMS 2.0 and in Remote Client Installation with the Topology, client, and client operating systems network discovery option turned on, computers may be discovered but may not be installed.
Network security: Lan Manager authentication level
Background LAN Manager (LM) authentication is the protocol that is used to authenticate Windows clients for network operations, including domain joins, accessing network resources, and user or computer authentication. The LM authentication level determines which challenge/response authentication protocol is negotiated between the client and the server computers. Specifically, the LM authentication level determines which authentication protocols that the client will try to negotiate or that the server will accept. The value that is set for LmCompatibilityLevel determines which challenge/response authentication protocol is used for network logons. This value affects the level of authentication protocol that clients use, the level of session security negotiated, and the level of authentication accepted by servers. Possible settings include the following.
| Value | Setting | Description |
|---|---|---|
| 0 | Send LM & NTLM responses | Clients use LM and NTLM authentication and never use NTLMv2 session security. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 1 | Send LM & NTLM - use NTLMv2 session security if negotiated | Clients use LM and NTLM authentication, and use NTLMv2 session security if the server supports it. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 2 | Send NTLM response only | Clients use NTLM authentication only and use NTLMv2 session security if the server supports it. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 3 | Send NTLMv2 response only | Clients use NTLMv2 authentication only and use NTLMv2 session security if the server supports it. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 4 | Send NTLMv2 response only/refuse LM | Clients use NTLMv2 authentication only and use NTLMv2 session security if the server supports it. Domain controllers refuse LM and accept only NTLM and NTLMv2 authentication. |
| 5 | Send NTLMv2 response only/refuse LM & NTLM | Clients use NTLMv2 authentication only and use NTLMv2 session security if the server supports it. Domain controllers refuse LM and NTLM and accept only NTLMv2 authentication. |
Note In Windows 95, Windows 98, and Windows 98 Second Edition, the Directory Services Client uses SMB signing when it authenticates with Windows Server 2003 servers by using NTLM authentication. However, these clients do not use SMB signing when they authenticate with these servers by using NTLMv2 authentication. Additionally, Windows 2000 servers do not respond to SMB signing requests from these clients. Check the LM authentication level: You must change the policy on the server to permit NTLM, or you must configure the client computer to support NTLMv2. If the policy is set to (5) Send NTLMv2 response only\refuse LM & NTLM on the target computer that you want to connect to, you must either lower the setting on that computer or set the security to the same setting that is on the source computer that you are connecting from. Find the correct location where you can change the LAN manager authentication level to set the client and the server to the same level. After you find the policy that is setting the LAN manager authentication level, if you want to connect to and from computers that are running earlier versions of Windows, lower the value to at least (1) Send LM & NTLM - use NTLM version 2 session security if negotiated. One effect of incompatible settings is that if the server requires NTLMv2 (value 5), but the client is configured to use LM and NTLMv1 only (value 0), the user who tries authentication experiences a logon failure that has a bad password and that increments the bad password count. If account lock-out is configured, the user may eventually be locked out. For example, you may have to look on the domain controller, or you may have to examine the domain controller's policies. Look on the domain controller Note You may have to repeat the following procedure on all the domain controllers.
Click Start , point to Programs , and then click Administrative Tools .
Under Local Security Settings , expand Local Policies .
Click Security Options .
Double-click Network Security: LAN manager authentication level , and then click a value in the list.
If the Effective Setting and the Local Setting are the same, the policy has been changed at this level. If the settings are different, you must check the domain controller's policy to determine whether the Network Security: LAN manager authentication level setting is defined there. If it is not defined there, examine the domain controller's policies. Examine the domain controller's policies
In the Domain Controller Security policy, expand Security Settings , and then expand Local Policies .
Double-click Network Security: LAN manager authentication level, and then click a value in the list.
You may also have to check policies that are linked at the site level, the domain level, or the organizational unit (OU) level to determine where you must configure the LAN manager authentication level.
If you implement a Group Policy setting as the default domain policy, the policy is applied to all computers in the domain.
If you implement a Group Policy setting as the default domain controller's policy, the policy applies only to the servers in the domain controller's OU.
It is a good idea to set the LAN manager authentication level in the lowest entity of necessary scope in the policy application hierarchy.
Windows Server 2003 has a new default setting to use NTLMv2 only. By default, Windows Server 2003 and Windows 2000 Server SP3-based domain controllers have enabled the "Microsoft network server: Digitally sign communications (always)" policy. This setting requires the SMB server to perform SMB packet signing. Changes to Windows Server 2003 were made because domain controllers, file servers, network infrastructure servers, and Web servers in any organization require different settings to maximize their security. If you want to implement NTLMv2 authentication in your network, you must make sure that all the computers in the domain are set to use this authentication level. If you apply Active Directory Client Extensions for Windows 95 or Windows 98 and Windows NT 4.0, the client extensions use the improved authentication features that are available in NTLMv2. Because client computers that are running any of the following operating system are not affected by Windows 2000 Group Policy Objects, you may have to manually configure these clients:
Microsoft Windows NT 4.0
Microsoft Windows Millennium Edition
Microsoft Windows 98
Microsoft Windows 95
Note If you enable the Network security: Do not store LAN manager hash value on next password change policy or set the NoLMHash registry key, Windows 95-based and Windows 98-based clients that do not have the Directory Services Client installed cannot log on to the domain after a password change. Many third-party CIFS servers, such as Novell Netware 6, are not aware of NTLMv2 and use NTLM only. Therefore, levels greater than 2 do not permit connectivity. There also are third-party SMB clients that do not use extended session security. In these cases, the LmCompatiblityLevel of the resource server is not taken into consideration. The server then packs up this legacy request and sends it to the User Domain Controller. The settings on the Domain Controller then decide what hashes are used to verify the request and whether these are meeting the Domain Controller's security requirements.
299656 How to prevent Windows from storing a LAN manager hash of your password in Active Directory and local SAM databases
2701704 Audit event shows authentication package as NTLMv1 instead of NTLMv2 For more information about LM authentication levels, click the following article number to view the article in the Microsoft Knowledge Base:
239869 How to enable NTLM 2 authentication
Nonrestrictive settings that send passwords in cleartext and that deny NTLMv2 negotiation
Restrictive settings that prevent incompatible clients or domain controllers from negotiating a common authentication protocol
Requiring NTLMv2 authentication on member computers and domain controllers that are running versions of Windows NT 4.0 that are earlier than Service Pack 4 (SP4)
Requiring NTLMv2 authentication on Windows 95 clients or on Windows 98 clients that do not have the Windows Directory Services Client installed.
If you click to select the Require NTLMv2 session security check box in the Microsoft Management Console Group Policy Editor snap-in on a Windows Server 2003 or Windows 2000 Service Pack 3-based computer, and you lower the LAN manager authentication level to 0, the two settings conflict, and you may receive the following error message in the Secpol.msc file or the GPEdit.msc file:
Windows cannot open the local policy database. An unknown error occurred when attempting to open the database.
For more information about the Security Configuration and Analysis Tool, see the Windows 2000 or the Windows Server 2003 Help files.
Reasons to Modify This Setting
You want to increase the lowest common authentication protocol that is supported by clients and domain controllers in your organization.
Where secure authentication is a business requirement, you want to disallow negotiation of the LM and the NTLM protocols.
Reasons to disable this setting Client or server authentication requirements, or both, have been increased to the point where authentication over a common protocol cannot occur.
Symbolic Name: LmCompatibilityLevel
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\LmCompatibilityLevel
Windows Server 2003: By default, the Windows Server 2003 NTLMv2 Send NTLM responses setting is enabled. Therefore, Windows Server 2003 receives the "Access Denied" error message after the initial installation when you try to connect to a Windows NT 4.0-based cluster or to LanManager V2.1-based servers, such as OS/2 Lanserver. This issue also occurs if you try to connect from an earlier-version client to a Windows Server 2003-based server.
You install Windows 2000 Security Rollup Package 1 (SRP1).SRP1 forces NTLM version 2 (NTLMv2). This rollup package was released after the release of Windows 2000 Service Pack 2 (SP2).
Windows 7 and Windows Server 2008 R2: Many third-party CIFS servers, such as Novell Netware 6 or Linux-based Samba servers, are not aware of NTLMv2 and use NTLM only. Therefore, levels greater than "2" do not permit connectivity. Now in this version of the operating system, the default for LmCompatibilityLevel was changed to "3". So when you upgrade Windows, these third party filers may stop working.
Microsoft Outlook clients may be prompted for credentials even though they are already logged on to the domain. When users supply their credentials, they receive the following error message: Windows 7 and Windows Server 2008 R2
The logon credentials supplied were incorrect. Make sure your username and domain are correct, then type your password again.
When you start Outlook, you may be prompted for your credentials even if your Logon Network Security setting is set to Passthrough or to Password Authentication. After you type your correct credentials, you may receive the following error message:
The login credentials supplied were incorrect.
A Network Monitor trace may show that the global catalog issued a remote procedure call (RPC) fault with a status of 0x5. A status of 0x5 means "Access Denied."
Windows 2000: A Network Monitor capture may show the following errors in the NetBIOS over TCP/IP (NetBT) server message block (SMB) session:
SMB R Search Directory Dos error, (5) ACCESS_DENIED (109) STATUS_LOGON_FAILURE (91) Invalid user identifier
Windows 2000: If a Windows 2000 domain with NTLMv2 Level 2 or later is trusted by a Windows NT 4.0 domain, Windows 2000-based member computers in the resource domain may experience authentication errors.
Windows 2000 and Windows XP: By default, Windows 2000 and Windows XP set the LAN Manager Authentication Level Local Security Policy option to 0. A setting of 0 means "Send LM and NTLM responses." Note Windows NT 4.0-based clusters must use LM for administration.
Windows 2000: Windows 2000 clustering does not authenticate a joining node if both nodes are part of a Windows NT 4.0 Service Pack 6a (SP6a) domain.
The IIS Lockdown Tool (HiSecWeb) sets the LMCompatibilityLevel value to 5 and the RestrictAnonymous value to 2.
Services for Macintosh User Authentication Module (UAM): The Microsoft UAM (User Authentication Module) provides a method for encrypting the passwords that you use to log on to Windows AFP (AppleTalk Filing Protocol) servers. The Apple User Authentication Module (UAM) provides only minimal or no encryption. Therefore, your password could easily be intercepted on the LAN or on the Internet. Although the UAM is not required, it does provide encrypted authentication to Windows 2000 Servers that run Services For Macintosh. This version includes support for NTLMv2 128-bit encrypted authentication and a MacOS X 10.1-compatible release. By default, the Windows Server 2003 Services for Macintosh server permits only Microsoft Authentication.
Windows Server 2008, Windows Server 2003, Windows XP, and Windows 2000: If you configure the LMCompatibilityLevel value to be 0 or 1 and then configure the NoLMHash value to be 1, applications and components may be denied access through NTLM. This issue occurs because the computer is configured to enable LM but not to use LM-stored passwords. If you configure the NoLMHash value to be 1, you must configure the LMCompatibilityLevel value to be 2 or higher.
Network security: LDAP client signing requirements
Background The Network security: LDAP client signing requirements setting determines the level of data signing that is requested on behalf of clients that issue Lightweight Directory Access Protocol (LDAP) BIND requests as follows:
None: The LDAP BIND request is issued with the caller-specified options.
Negotiate signing: If the Secure Sockets Layer/Transport Layer Security (SSL/TLS) has not been started, the LDAP BIND request is initiated with the LDAP data signing option set in addition to the caller-specified options. If SSL/TLS has been started, the LDAP BIND request is initiated with the caller-specified options.
Require signing: This is the same as Negotiate signing. However, if the LDAP server's intermediate saslBindInProgress response does not indicate that LDAP traffic signing is required, the caller is told that the LDAP BIND command request failed.
Risky configuration Enabling the Network security: LDAP client signing requirements setting is a harmful configuration setting. If you set the server to require LDAP signatures, you must also configure LDAP signing on the client. Not configuring the client to use LDAP signatures will prevent communication with the server. This causes user authentication, Group Policy settings, logon scripts, and other features to fail.
Reasons to Modify This Setting Unsigned network traffic is susceptible to man-in-the-middle attacks where an intruder captures packets between the client and the servers, modifies them, and then forwards them to the server. When this occurs on an LDAP server, an attacker could cause a server to respond based on false queries from the LDAP client. You can lower this risk in a corporate network by implementing strong physical security measures to help protect the network infrastructure. Additionally, you can help prevent all kinds of man-in-the-middle attacks by requiring digital signatures on all network packets by means of IPSec authentication headers.
Symbolic Name: LDAPClientIntegrity
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LDAP\LDAPClientIntegrity
Event Log: Maximum security log size
Background The Event Log: Maximum security log size security setting specifies the maximum size of the security event log. This log has a maximum size of 4 GB. To locate this setting, expand Windows Settings , and then expand Security Settings .
Restricting the security log size and the security log retention method when the Audit: Shut down system immediately if unable to log security audits setting is enabled. See the "Audit: Shut down system immediately if unable to log security audits" section of this article for more details.
Restricting the security log size so that security events of interest are overwritten.
Reasons to Increase This Setting Business and security requirements may dictate that you increase the security log size to handle additional security log detail or to retain security logs for a longer period of time.
Reasons to Decrease This Setting Event Viewer logs are memory mapped files. The maximum size of an event log is constrained by the amount of physical memory in the local computer and by the virtual memory that is available to the event log process. Increasing the log size beyond the amount of virtual memory that is available to Event Viewer does not increase the number of log entries that are maintained.
Examples of compatibility problems Windows 2000: Computers that are running versions of Windows 2000 that are earlier than Service Pack 4 (SP4) may stop logging events in the event log before reaching the size that is specified in the Maximum log size setting in Event Viewer if the Do not overwrite events (clear log manually) option is turned on.
Event Log: Retain security log
Background The Event Log: Retain security log security setting determines the "wrapping" method for the security log. To locate this setting, expand Windows Settings , and then expand Security Settings .
Failing to retain all logged security events before they are overwritten
Configuring the Maximum security log size setting too small so that security events are overwritten
Restricting the security log size and retention method while the Audit: Shut down system immediately if unable to log security audits security setting is enabled
Reasons to enable this setting Enable this setting only if you select the Overwrite events by days retention method. If you use an event correlation system that polls for events, make sure that the number of days is at least three times the poll frequency. Do this to allow for failed poll cycles.
Network access: Let Everyone permissions apply to anonymous users
Background By default, the Network access: Let Everyone permissions apply to anonymous users setting is set to Not Defined on Windows Server 2003. By default, Windows Server 2003 does not include the Anonymous Access token in the Everyone group.
Example of Compatibility Problems The following value of
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA\everyoneincludesanonymous [REG_DWORD]=0x0 breaks trust creation between Windows Server 2003 and Windows NT 4.0, when the Windows Server 2003 domain is the account domain and the Windows NT 4.0 domain is the resource domain. This means that the account domain is Trusted on Windows NT 4.0 and the resource domain is Trusting on the Windows Server 2003 side. This behavior occurs because the process to start the trust after the initial anonymous connection is ACL'd with the Everyone token that includes the Anonymous SID on Windows NT 4.0.
Reasons to Modify This Setting The value must be set to 0x1 or set by using a GPO on the domain controller's OU to be: Network access: Let Everyone permissions apply to anonymous users - Enabled to make the trust creations possible. Note Most other security settings go up in value instead of down to 0x0 in their most secured state. A more secure practice would be to change the registry on the primary domain controller emulator instead of on all the domain controllers. If the primary domain controller emulator role is moved for any reason, the registry must be updated on the new server. A restart is required after this value is set.
Registry Path
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA\everyoneincludesanonymous
NTLMv2 authentication
Session security Session security determines the minimum security standards for client and server sessions. It is a good idea to verify the following security policy settings in the Microsoft Management Console Group Policy Editor snap-in:
Computer Settings\Windows Settings\Security Settings\Local Policies\Security Options
Network Security: Minimum session security for NTLM SSP based (including secure RPC) servers
Network Security: Minimum session security for NTLM SSP based (including secure RPC) clients
The options for these settings are as follows:
Require message integrity
Require message confidentiality
Require NTLM version 2 session security
Require 128-bit encryption
The default setting prior to Windows 7 is No requirements. Starting with Windows 7, the default changed to Require 128-bit encryption for improved security. With this default, legacy devices that don’t support 128-bit encryption will be unable to connect. These policies determine the minimum security standards for an application-to-application communications session on a server for a client. Note that although described as valid settings, the flags to require message integrity and confidentiality are not used when the NTLM session security is determined. Historically, Windows NT has supported the following two variants of challenge/response authentication for network logons:
LM challenge/response
NTLM version 1 challenge/response
LM allows interoperability with the installed base of clients and servers. NTLM provides improved security for connections between clients and servers. The corresponding registry keys are as follows:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\MSV1_0\"NtlmMinServerSec" HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa\MSV1_0\"NtlmMinClientSec"
Risky configurations This setting controls how network sessions secured using NTLM will be handled. This affects RPC-based sessions authenticated with NTLM, for example. There are the following risks:
Using older authentication methods than NTLMv2 makes the communication easier to attack due to the simpler hashing methods used.
Using encryption keys lower than 128-bit allows attackers to break communication using brute-force attacks.
Time synchronization
Time synchronization failed. The time is off by more than 30 minutes on an affected computer. Make sure that the client computer's clock is synchronized with the domain controller's clock.
Workaround for SMB signing
We recommend that you install Service Pack 6a (SP6a) on Windows NT 4.0 clients that interoperate in a Windows Server 2003-based domain. Windows 98 Second Edition-based clients, Windows 98-based clients, and Windows 95-based clients must run the Directory Services Client to perform NTLMv2. If Windows NT 4.0-based clients do not have Windows NT 4.0 SP6 installed or if Windows 95-based clients, Windows 98-based clients, and Windows 98SE-based clients do not have the Directory Services Client installed, disable SMB signing in the default domain controller's policy setting on the domain controller's OU, and then link this policy to all OUs that host domain controllers. The Directory Services Client for Windows 98 Second Edition, Windows 98, and Windows 95 will perform SMB Signing with Windows 2003 servers under NTLM authentication, but not under NTLMv2 authentication. Additionally, Windows 2000 servers will not respond to SMB Signing requests from these clients. Although we do not recommend it, you can prevent SMB signing from being required on all domain controllers that run Windows Server 2003 in a domain. To configure this security setting, follow these steps:
Open the default domain controller's policy.
Open the Computer Configuration\Windows Settings\Security Settings\Local Policies\Security Options folder.
Locate and then click the Microsoft network server: Digitally sign communications (always) policy setting, and then click Disabled.
Important This section, method, or task contains steps that tell you how to modify the registry. However, serious problems might occur if you modify the registry incorrectly. Therefore, make sure that you follow these steps carefully. For added protection, back up the registry before you modify it. Then, you can restore the registry if a problem occurs. For more information about how to back up and restore the registry, click the following article number to view the article in the Microsoft Knowledge Base:
322756 How to back up and restore the registry in Windows Alternatively, turn off SMB signing on the server by modifying the registry. To do this, follow these steps:
Click Start , click Run , type regedit, and then click OK .
Locate and then click the following subkey: HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\Lanmanserver\Parameters
Click the enablesecuritysignature entry.
On the Edit menu, click Modify .
In the Value data box, type 0, and then click OK .
Exit Registry Editor.
Restart the computer, or stop and then restart the Server service. To do this, type the following commands at a command prompt, and then press Enter after you type each command: net stop server net start server
Note The corresponding key on the client computer is in the following registry subkey:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Lanmanworkstation\Parameters The following lists the translated error code numbers to status codes and to the verbatim error messages that are mentioned earlier:
error 5 ERROR_ACCESS_DENIED Access is denied.
error 1326 ERROR_LOGON_FAILURE Logon failure: unknown user name or bad password.
error 1788 ERROR_TRUSTED_DOMAIN_FAILURE The trust relationship between the primary domain and the trusted domain failed.
error 1789 ERROR_TRUSTED_RELATIONSHIP_FAILURE The trust relationship between this workstation and the primary domain failed.
For more information, click the following article numbers to view the articles in the Microsoft Knowledge Base:
324802 How to configure Group Policies to set security for system services in Windows Server 2003
816585 How to apply predefined security templates in Windows Server 2003

Need more help?
Want more options.
Explore subscription benefits, browse training courses, learn how to secure your device, and more.

Microsoft 365 subscription benefits

Microsoft 365 training

Microsoft security

Accessibility center
Communities help you ask and answer questions, give feedback, and hear from experts with rich knowledge.

Ask the Microsoft Community

Microsoft Tech Community

Windows Insiders
Microsoft 365 Insiders
Was this information helpful?
Thank you for your feedback.
Stack Exchange Network
Stack Exchange network consists of 183 Q&A communities including Stack Overflow , the largest, most trusted online community for developers to learn, share their knowledge, and build their careers.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
What is the relationship between User Rights Assignment Policies vs. Membership of Local Groups
I just spent the better part of this morning on a support call with a vendor where we eventually resolved our issue by manually adding the service account their application was using to the following Computer Configuration/Policies/Windows Settings/Security Settings/Local Policies/User Rights Assignment policies which were being set by a Domain GPO:
- Back up files and directories
- Log on as a batch job
- Restore files and directories
After rebooting the server and getting the updated GPO our service account no longer generated the following Event 4625 - Logon Type 4 audit events when attempting to start the application:
The vendor's documentation instructed us to add the service account to the Backup Operators and Power User Local Groups - which we did. Reading the Explain tab for each one of the required User Right Assignment policies indicates that the Backup Operators have those Rights by default (TechNet seems to confirm this ). Incidentally, there's no mention of Power User being assigned those Rights that I can find so I'm not really sure why that was a requirement.
Why did we have to explicitly assign that service account those Rights ( Back up files and directories , Log on as a batch job , Restore files and directories ) when it already should of had them by virtue of being a member of the Backup Operators Local Group?
What is the relation between the User Rights Policies and the builtin Local Groups? Are User Rights Polices the constituent parts that make up the "meta"-rights of each builtin Local Groups? If so, where can I find which Rights belong to which bultin Local Groups?
As stated we resolved this issue by adding our service account to the Group Policy Object that is manually assigning a number of service accounts these specific Rights. I got the sense from the vendor's engineer that this GPO is interfering with the mapping of these constituent Rights to Local Groups. Is this hunch correct? Is assigning constituent User Rights this way a Bad Idea (TM)?
- windows-server-2008-r2
- group-policy
- windows-authentication
Members of local built-in groups (as well as domain groups) have whatever rights are assigned to the group. The default rights on a server for local built-in groups are set in the local security settings. To access the local security settings, click Start, type secpol.msc and hit enter. In the Local Security Policy editor, expand Local Policies, and click on User Rights Assignment. There you will see what groups/users are granted which rights.
The local User Rights Assignment settings can be overriden by domain group policy. If you create a domain group policy that grants certain groups/users a certain right, such as "Logon as a batch job", this will override the local policy for which users have that right.
From what you have written, here is what I am guessing happened: You had a GPO in your domain that granted certain users the rights that you mentioned. This policy did not grant these rights to local machine Backup Operators group. This policy overwrote the default policy on the server. Thus, adding the user to the Backup Operators group did not give them those rights because, due to the Domain GPO, the Backup Operators do not have them.
As to whether or not the vendor's solution is a good idea: I have found that it is usually easier to manage rights by using well-organized groups rather than granting them to individual accounts. This way, when you add a new user, you add the user to the logical groups to which he belongs, and he will immediately have all of the rights he needs rather than having to assign him each right one-by-one. That is what the Built-in groups were intended to do.
Instead of granting those three rights to an individual user, you could have granted the "Backup Operators" group those three rights in the GPO. Then adding the user to that group would have the intended effect.
I am curious why you would have a domain policy managing those rights in the first place. If the purpose was to grant certain users access to perform backup operations, it might have been a better idea to use the domain built-in Backup Operators group.
You must log in to answer this question.
- Featured on Meta
- Site maintenance - Tuesday, July 23rd 2024, 8 PM - Midnight EST (3 AM - 7 AM...
- Announcing a change to the data-dump process
- Upcoming initiatives on Stack Overflow and across the Stack Exchange network...
Hot Network Questions
- How does Biden staying in the presidential race hurt Democrats in Congress?
- Why are the categories of category theory called "category"?
- Rudimentary black jack game implementation
- The shortest way from A1 to B1
- A dual space to a space of homogeneous polynomials
- Is "avoid extra null pointer risk" a reason to avoid "introduce parameter objects"?
- When Page Lock happen under Read Committed Isolation level in SQL Server
- Hardware serial baudrate inconsistent between Arduino nano and standalone 328P
- What happens to a sparse file's holes when the space is needed?
- Is “faith” sometimes a work by us, and sometimes a work of God?
- Initializing a map container only if it is not already initialized in Leaflet
- Is a stiff chain after hot wax application a sign of a correct wax application?
- Has D. Trump mentioned whether he'd be willing to debate K. Harris?
- Is there any way for a character to identify another character's class?
- Help understanding lines 7 & 8 from Shakespeare's 18th sonnet
- Using a dynamo hub to run ONLY rear lights
- How compute a BIC for multivariate regression?
- ID a book about siblings forced to become part of evil family and take care of dragons
- On a trigonometric inequality by Huygens
- Lemma's taking value of succeeding theorem
- Are consumable material components consumed if the spell fails?
- How to address past academic misconduct as a new faculty member?
- Should I write and commit unit tests for minor changes and bug fixes?
- Choice of Generalized Coordinates
All about Microsoft Intune
Peter blogs about Microsoft Intune, Microsoft Intune Suite, Windows Autopilot, Configuration Manager and more
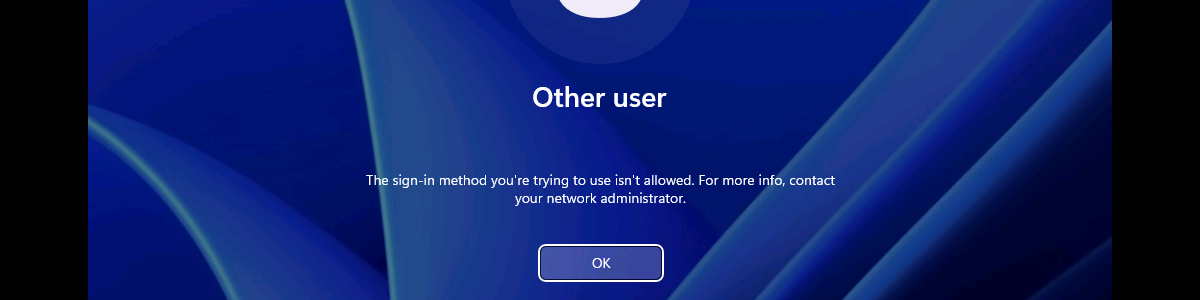
Restricting the local log on to specific users
This week is about restricting the local logon on Windows devices to specific users. Not because it is something particularly new, but simply because it is been an ask every now and then. Think about further locking down a kiosk device, for example. Restricting the local logon can be achieved by either only allowing specific users to log on, or by denying specific users to log on. In other words, whitelisting versus blacklisting. The allow-option is basically a whitelist and the deny-option is basically a blacklist. When looking at restricting the local logon, a whitelist is the easiest method to get quickly really restrictive, as only the users on the list are allowed to log on locally. Luckily, nowadays there is easy method for configuring such a whitelist with users that are allowed to log on locally on a Windows device. This post will provide some more details around that configuration, followed with the configuration steps. This post will end with showing the user experience.
Note : Keep in mind that this post is focussed on the local log on on Windows devices and not the remote log on.
Configuring the allow local log on setting
When looking at configuring the allow local log on configuration, the UserRights section in the Policy CSP is the place to look. That section contains many of the different policy settings of the User Rights Assignment Local Policies , including the Allow log on locally ( AllowLocalLogOn ) policy setting. That policy setting can be used to configure the users that are allowed to locally log on to the Windows device. Besides that, it’s also good to mention that with the latest Windows 11 Insider Preview Builds, this section of the Policy CSP, is getting more and more policy settings. Nearly all of the User Rights Assignment Local Policies are now available for configuration, including Logon as a service , Logon as a batch job , and many more. Maybe even better, all of these available policy settings – including the new policy settings that are currently still in preview – are now configurable via the Settings Catalog profile (as shown below in Figure 1).
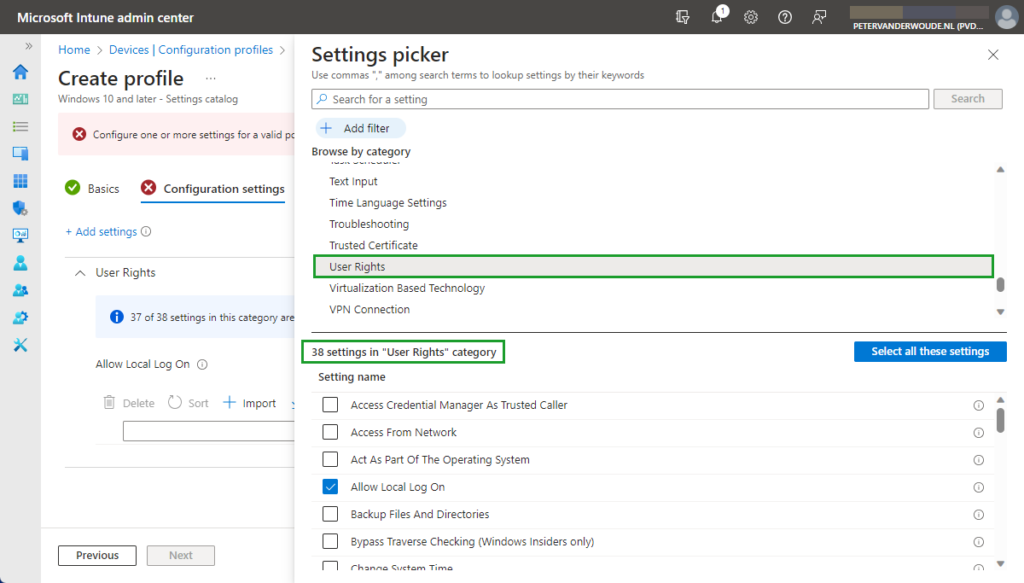
After being familiar with the available policy settings and the configuration profile, the configuration of those policy settings is pretty straight forward. The following eight steps walk through the creation of a Settings Catalog profile that contains the required setting to configure the local logon, by using the Allow log on locally policy setting.
- Open the Microsoft Intune admin center portal and navigate to Devices > Windows > Configuration profiles
- On the Windows | Configuration profiles blade, click Create profile
- On the Create a profile blade, provide the following information and click Create
- Platform : Select Windows 10 and later to create a profile for Windows 10 and Windows 11 devices
- Profile : Select Settings catalog to select the required setting from the catalog
- On the Basics page, provide the following information and click Next
- Name : Provide a name for the profile to distinguish it from other similar profiles
- Description : (Optional) Provide a description for the profile to further differentiate profiles
- Platform : (Greyed out) Windows 10 and later
- On the Configuration settings page, as shown below in Figure 2, perform the following actions
- Select User Rights as category
- Select Allow Local Log On as setting
- Specify the required users and local groups – all on separate lines – and click Next
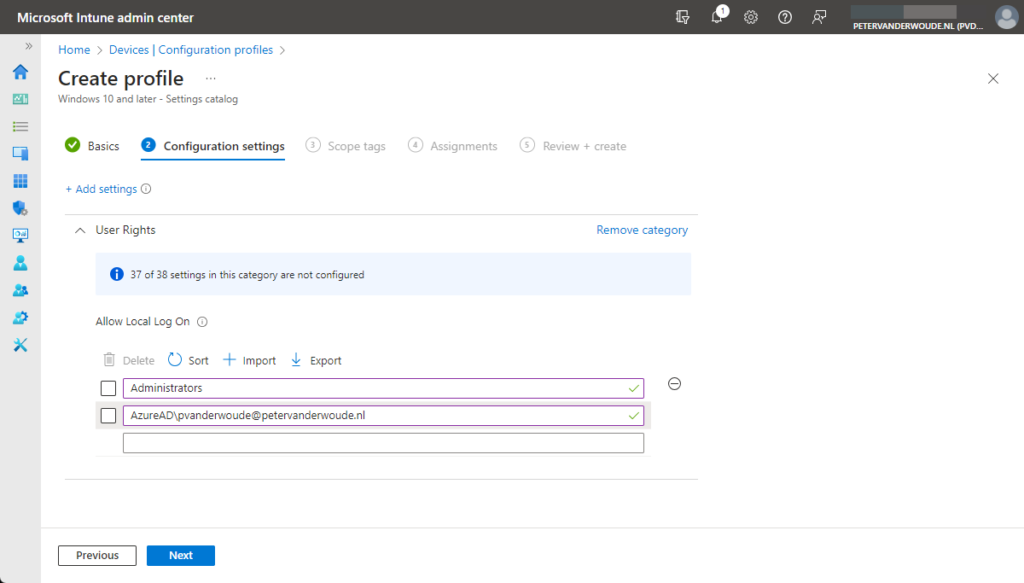
- On the Scope tags page, configure the required scope tags and click Next
- On the Assignments page, configure the assignment and click Next
- On the Review + create page, verify the configuration and click Create
Note : As these settings are now configurable via the Settings Catalog , that also takes away the challenges with multiple entries. No need to manually specify a delimiter, as Microsoft Intune takes care of that.
Experiencing the user rights configuration
After configuring the users that are allowed to log on locally to the Windows device, it’s pretty straight forward to experience the behavior. Simply try to log on to that device with a user account that is not allowed to log on locally. That will provide an experience as shown below in Figure 3. The user will receive the notification that the sign-in method is not allowed. Besides that, it’s also important to be familiar with the side effects of this configuration. The most important side effect is the impact on the self-service capabilities, like self-service PIN reset and self-service password reset. That’s simply because those capabilities rely on the temporary account defaultuser1 and that account won’t be able to log in, as only the specified users are allowed to locally log on to the Windows device. That experience is shown below in Figure 4. The user will either receive the status message of 0xc000015b , or will simply be switched back to the logon screen.
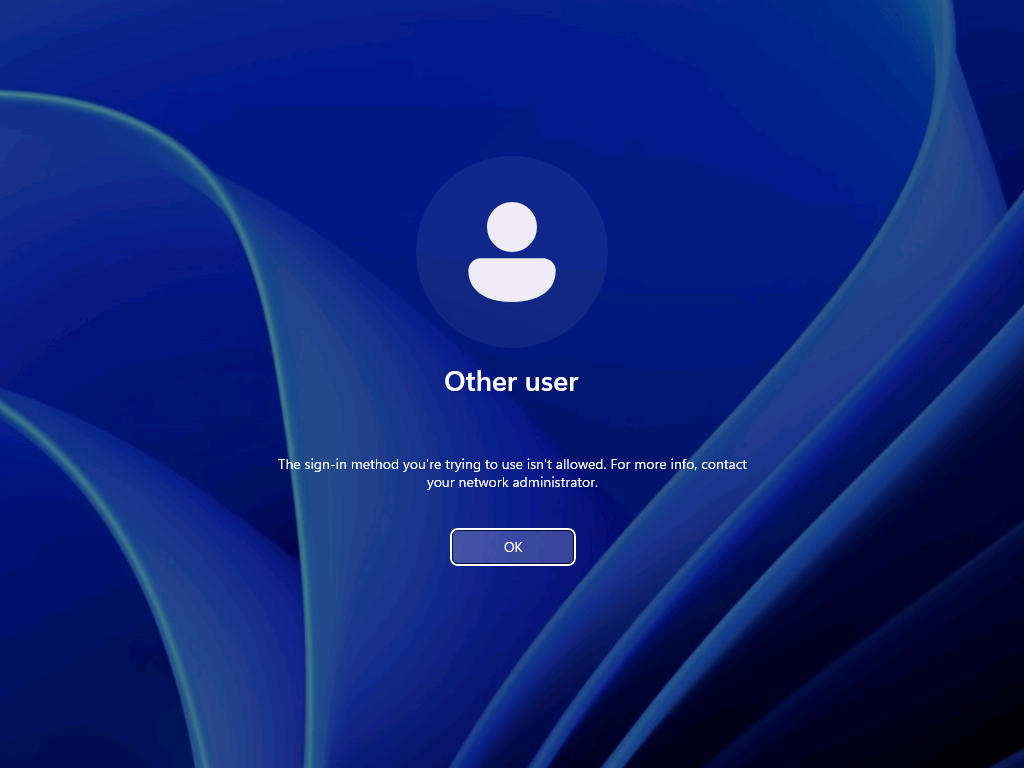
Note : The failed log on information is registered in the Security log in the Event Viewer with Event ID 4625 .
More information
For more information about the user rights configuration options, refer to the following docs.
- UserRights Policy CSP – Windows Client Management | Microsoft Learn
- Self-service password reset for Windows devices – Microsoft Entra | Microsoft Learn
31 thoughts on “Restricting the local log on to specific users”
I’d like to contribute to this.
This method does not inherently allow you to specify an EntraID group of users that you wish to deny local logon (at least it didnt use to) however i’ve found that if you use “account protection” policies populate the local group “Guests” with users from an EntraID group you can use the above stated policy to in effect acheive deny local logon for an EntraID group of users. (Via denying the local group “guests” as stated in your blog)
I use this in production, works well
Thank you for that suggestion, Temilit. Regards, Peter
I have not been able to replicate this. I followed inthecloud247’s blog post on this, but the only SID I was able to add to the Guests local group was the SID of an AAD directory role, and not one of an AAD security group.
Which version of Windows are you using? Regards, Peter
- Pingback: Microsoft Roadmap, messagecenter en blogs updates van 21-09-2023 - KbWorks
Can you use an AAD group here?
Not at this moment, Henrik. Regards, Peter
Is there currently a way to restrict interactive log in but allow elevation log in prompts? I would like to prevent Intune Admins from logging in locally but still allow elevation for installs/CMD.
Not sure you can achieve that with this policy, but I haven’t looked really deep in that use case yet. Regards, Peter
- Pingback: Intune Newsletter - 22nd September 2023 - Andrew Taylor
- Pingback: Enabling remote access for specific users on Azure AD joined devices – All about Microsoft Intune
Is there a way to specify an EntraID security group with this settings?
Hi Yoni, The last time I tried that was not possible yet. Regards, Peter
Is there a way sign in KioskUser0 automatically using User Rights?
Hi Mo, Can you provide some more details about what you’re trying to achieve? Regards, Peter
We have deployed Self-Deploy AutoPilot profile plus Kiosk Configuration Profile for single app and then assign to dynamic device group. The Self-Deploy AutoPilot process completes without any issues and Kiosk policy is applied to the device. However, the KioskUser0 should auto logging automatically after Self-Deploy AutoPilot process completes, but its not auto logging.
Any thought why KioskUser0 not auto logging automatically?
Hi Mo, That can be many things, but something I often see is the device lock configuration that is interfering. Regards, Peter
Hello Peter,
We have Azure AD Joined devices in our enviornment which are migrated from source tenant to target tenant as part of carve out project. Recently we observed that post autopilot build completition when user tried to sign in to device they were prompted error as Sign in method not allowed. However, if we tried to login to device with local admins then it allows.
Standard users not allowed to login, we do have AllowLocallyLogIn baseline policy deployed by security team but it contains Administrators and Users group both. Does on Azure AD joined devices this policy really gets validated when users trying to sign in with UPN ?
This issue is not for all users but 10% users are facing, as a workaround when we reimported hash of thier device again and reimaged device then sign in was allowed (bit strange).
Do you have any idea on this then please give some direction.
Hi Suraj, How did you migrate the devices from source tenant to the target tenant? Regards, Peter
I am seeing something similar for new devices. Again, not all, only a subset. quite often, the user can happily use the device for a period (a few days) then this occurs. LOgging onto the device locally, I am seeing the Allow Logon Locally being blank. very odd. This is using Windows 11 23H2
Hi Shaun, When that happens, do you see anything about (other) policies being applied and/or change? Regards, Peter
I tried to do the restriction as in your procedure, but I got the error 65000 in intune. Since then, it has been impossible to connect with ALL the accounts on the computer. Do you have a solution to go back?
Hi Simon, In that case, you should apply a counter policy with the default configuration. Regards, Peter
Hello, What do you mean when you say “you should apply a counter policy with the default configuration” ? Can you post a screenshot ?
Regards Olivier
Hi Olivier, I mean that you should configure the same policy, but with the default configuration that is available on the devices within your environment. Regards, Peter
I’ve had a similar issue. What would the correct counter policy be to reset the default logon configuration or do you have an article that details that?
Hi Mike, Easiest is to check a different device an see what the default configuration is. Regards, Peter
I know this has been a bit since you created this article, but have you been able to automate the AllowLocalLogOn to only the primary user?
I’ve been looking into this my self, but I don’t seem to be able to automate it via policy. The only way seems to be script based?
That is correct. If you want to match it with the primary user, you would need to use some custom scripting. Regards, Peter
Is there a way to rollback this policy once implemented?
Hi Ninad, You can always counter the policy by configuring the original values. Regards, Peter
Leave a Comment Cancel reply
Notify me of follow-up comments by email.
Notify me of new posts by email.
This site uses Akismet to reduce spam. Learn how your comment data is processed .
The Windows Security Log Revealed

Chapter 10 Privilege Use Events
You can use the Privilege Use audit category to track the exercise of user rights. Microsoft uses the terms privilege, right, and permission inconsistently. In the case of this audit category, privilege refers to most of the user rights that you find in the Local Security Policy under Security Settings\Local Policies\User Rights Assignment — with one important exception. Intermingled within those user rights are logon rights. Logon rights such as Allow logon locally and Access this computer from the network are not addressed by the Privilege Use category because they aren’t technically user rights. (To find out when a logon right is exercised, you can refer to the Logon/Logoff category’s Logon subcategory, which we discussed in Chapter 5 ).

The chart below lists the subcategories of the Privilege Use category, along with the privileges that Microsoft considers Sensitive Privilege Use and Non Sensitive Privilege Use. We have not observed any events in the Non Sensitive Privilege Use subcategory, and most of the listed privileges in this category are not audited.
| Privilege Use Subcategories | Included Privileges |
| Sensitive Privilege Use | Act as part of the operating system Back up files and directories Create a token object Debug programs Enable computer and user accounts to be trusted for delegation Generate security audits Impersonate a client after authentication Load and unload device drivers Manage auditing and security log Modify firmware environment values Replace a process-level token Restore files and directories Take ownership of files or other objects |
| Non Sensitive Privilege Use | Access Credential Manager as a trusted caller Access this computer from the network Add workstations to domain Adjust memory quotas for a process Allow logon locally Allow logon through Terminal Services Bypass traverse checking Change the system time Create a pagefile Create global objects Create permanent shared objects Create symbolic links Deny access this computer from the network Deny log on as a batch job Deny log on as a service Deny log on locally Deny log on through Terminal Services Force shutdown from a remote system Increase a process working set Increase scheduling priority Lock pages in memory Log on as a batch job Log on as a service Modify an object label Perform volume maintenance tasks Profile single process Profile system performance Remove computer from docking station Shut down the system Synchronize directory service data |
| Other Privilege Use Events | No events in this subcategory |
The Privilege Use category logs two events.
| Event ID | Title |
|
| A privileged service was called |
|
| An operation was attempted on a privileged object |
For most user rights, Windows logs a Privilege Use event when a user exercises the right. However, some rights are exercised so frequently during the normal course of a user’s activities that the Security log would quickly fill if Windows were to log each use. Therefore Windows doesn’t normally log some rights. Among these high-use rights are Back up files and directories and Restore files and directories. You can force Windows to log these two rights by enabling the Audit: Audit the use of Backup and Restore privilege security option, but enabling this option will result in a Privilege Use event being logged for every single file, folder, and other object during system backups, overwhelming your log with events of questionable value.
Backup and Restore privileges are also used at other times, specifically whenever an application attempts access through the NTFS backup API. For normal user rights, Windows logs either event ID 4673 or event ID 4674 when right is exercised. As mentioned earlier, logon rights are never logged by Privilege Use events: The use of logon rights is documented by Logon/Logoff events. Event ID 4674 has to do with a privilege that is used to access an object. Therefore, this event lists the object name. Event ID 4673 lists the affected process and service name.
| System Name of Privilege | Description | Notes |
| SeTcbPrivilege | Act as part of the operating system | Logged frequently Event |
| SeMachineAccountPrivilege | Add workstations to domain | Not logged |
| SeBackupPrivilege | Back up files and directories | Logged only when the security option is enabled |
| SeCreatePermanentPrivilege | Create permanent shared objects |
|
| SeEnableDelegationPrivilege | Enable computer and user accounts to be trusted for delegation |
|
| SeRemoteShutdownPrivilege | Force shutdown from a remote system |
|
| SeLoadDriverPrivilege | Load and unload device drivers |
|
| SeRestorePrivilege | Restore files and directories | Logged only when the security option is enabled |
| SeSecurityPrivilege | Manage auditing and Security log | Event |
| SeShutdownPrivilege | Shut down the system | Event |
| SeTakeOwnershipPrivilege | Take ownership of files or other objects | Event
|
| SeIncreaseBasePriorityPrivilege | Increase Scheduling Priority | Event |
- ChangeNotifyPrivilege
- AuditPrivilege
- CreateTokenPrivilege
- AssignPrimaryTokenPrivilege
- BackupPrivilege
- RestorePrivilege
- DebugPrivilege
Bottom Line
The Privilege Use category generates a lot of noise, and we usually recommend leaving it disabled. In fact, Microsoft’s former Security log guru, Eric Fitzgerald , as much as says that this audit policy and its events are useless because no “central reference” of which operations are controlled by each privilege exists. That lack reduces the value of this category.
Next Chapter
Back to top
Setup PowerShell Audit Log Forwarding in 4 Minutes
| • | |
| • | |
| • | |
| • | |
| • | |
| • | |
| • | |
| • | |
| • | |
| • | Privilege Use |
| • | |
| • | |
| • |

- NIST 800-53
- Common Controls Hub
The Create global objects user right must only be assigned to Administrators, Service, Local Service, and Network Service.
| Finding ID | Version | Rule ID | IA Controls | Severity |
|---|---|---|---|---|
| V-73749 | WN16-UR-000100 | SV-88413r2_rule | Medium |
| Description |
|---|
| Inappropriate granting of user rights can provide system, administrative, and other high-level capabilities. Accounts with the "Create global objects" user right can create objects that are available to all sessions, which could affect processes in other users' sessions. |
| STIG | Date |
|---|---|
| 2019-12-12 |
| Check Text ( C-91481r1_chk ) |
|---|
| Verify the effective setting in Local Group Policy Editor. Run "gpedit.msc". Navigate to Local Computer Policy >> Computer Configuration >> Windows Settings >> Security Settings >> Local Policies >> User Rights Assignment. If any accounts or groups other than the following are granted the "Create global objects" user right, this is a finding. - Administrators - Service - Local Service - Network Service For server core installations, run the following command: Secedit /Export /Areas User_Rights /cfg c:\path\filename.txt Review the text file. If any SIDs other than the following are granted the "SeCreateGlobalPrivilege" user right, this is a finding. S-1-5-32-544 (Administrators) S-1-5-6 (Service) S-1-5-19 (Local Service) S-1-5-20 (Network Service) If an application requires this user right, this would not be a finding. Vendor documentation must support the requirement for having the user right. The requirement must be documented with the ISSO. The application account must meet requirements for application account passwords, such as length (WN16-00-000060) and required frequency of changes (WN16-00-000070). |
| Fix Text (F-80199r1_fix) |
|---|
| Configure the policy value for Computer Configuration >> Windows Settings >> Security Settings >> Local Policies >> User Rights Assignment >> "Create global objects" to include only the following accounts or groups: - Administrators - Service - Local Service - Network Service |
- Stack Overflow for Teams Where developers & technologists share private knowledge with coworkers
- Advertising & Talent Reach devs & technologists worldwide about your product, service or employer brand
- OverflowAI GenAI features for Teams
- OverflowAPI Train & fine-tune LLMs
- Labs The future of collective knowledge sharing
- About the company Visit the blog

Collectives™ on Stack Overflow
Find centralized, trusted content and collaborate around the technologies you use most.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
Get early access and see previews of new features.
How to assign user rights to a local user account through powershell?
I want to modify the user rights associated with a local user account.I want to add groups and users to a particular User Rights. This is done by opening the group policy and opening the following folder in the console tree: Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment. Then click on the required user Right and add the user or group to it.
Is it possible to do the same through powershell scripts?
4 Answers 4
What I would do is open SecPol.msc, make your modifications via the GUI to a baseline computer and export an .inf template for installation via powershell.
The template can be installed with secedit.exe. If you want, you can open the inf file in a text editor and scroll until you see the [Privilege Rights] section. Here is one for example.
Run this command and reboot. Edit .inf and .db names as appropriate.
Found a third party command line solution. ntwrongs.exe
http://forums.mydigitallife.info/threads/57557-NTWrongs%99

Here is a purely powershell method - https://stackoverflow.com/a/26393118
To build upon @Knuckle-Dragger's answer:
I couldn't add my user to the secreatesymboliclinkprivilege setting ( Computer Configuration > Windows Settings > Security Settings > Local Policies > ** User Rights Assignment** > Create symbolic links ), always with the error "The specified domain either does not exist or could not be contacted", and it worked with his method, for my DOMAIN\user account from the whoami output:
Your Answer
Reminder: Answers generated by artificial intelligence tools are not allowed on Stack Overflow. Learn more
Sign up or log in
Post as a guest.
Required, but never shown
By clicking “Post Your Answer”, you agree to our terms of service and acknowledge you have read our privacy policy .
Not the answer you're looking for? Browse other questions tagged windows powershell or ask your own question .
- Featured on Meta
- Announcing a change to the data-dump process
- Site maintenance - Tuesday, July 23rd 2024, 8 PM - Midnight EST (3 AM - 7 AM...
- What makes a homepage useful for logged-in users
Hot Network Questions
- ELI5: If SSL encrypts traffic, why does it expire?
- Using a dynamo hub to run ONLY rear lights
- Use the decorate function and mark points on a curve to draw tangents
- Why is 負ける here used transitively?
- Why do Bell states have all real coefficients?
- Choice of Generalized Coordinates
- What drives the mechanical challenges which make trailing-edge flaps an (almost) ubiquitous solution vs leading-edge flaps?
- Rocket Nozzle Shape and Length
- What hidden class abilities are there in D&D 5e?
- How can a liability limitation in a contract between two parties prevent a damaged 3rd-party from taking action?
- MouseDown event
- Is a stiff chain after hot wax application a sign of a correct wax application?
- How to address past academic misconduct as a new faculty member?
- I found a counterexample to one of the intermediate assertions in a proof but not (necessarily) to the overall result – how to publish this?
- Has D. Trump mentioned whether he'd be willing to debate K. Harris?
- Shomer Negia in Case of Danger
- Spell slots of a Sorlock multiclass
- What happens to a sparse file's holes when the space is needed?
- Trump’s use of the term deportation
- Did firearm projectiles start being rifled before barrels?
- Braille-based Base64
- A dual space to a space of homogeneous polynomials
- Where is git-prompt.sh located in Ubuntu 24.04?
- Can 'as much as' be replaced by 'as well as' in 'Sam retorted that it was my fault as much as his.'?
- Knowledge Base
Policy Change Event: 608
The Who, Where and When information is very important for an administrator to have complete knowledge of all activities that occur on their Active Directory. This helps them identify any desired / undesired activity happening. ADAudit Plus assists an administrator with this information in the form of reports. In real-time, ensure critical resources in the network like the Domain Controllers are audited, monitored and reported with the entire information on AD objects - Users, Groups, GPO, Computer, OU, DNS, AD Schema and Configuration changes with 200+ detailed event specific GUI reports and email alerts.
Event ID 608 – User Right Assigned
| Event ID | 608 |
| Category | Policy Change |
| Type | Success Audit |
When there is a change to the user rights assignments on a computer, Windows logs event ID 608. Rights that are defined in group policy objects are applied by the computer.
The "User" field, meant to indicate the person who assigned or modified the rights, tends to show the name of the system. Thus, to determine the actual user who made the rights assignment changes, the domain controller's security logs must be checked.
Note: Event 608 is not logged for events such as "Access this computer from the network" or "Logon as a service".
This log data provides the following information:
- Assigned To
Why does event ID 608 need to be monitored?
- To monitor actions performed by the SYSTEM account
- To monitor the actions of high-value accounts
- To detect anomalies or malicious actions
- To ensure only whitelisted accounts perform certain actions
- To ensure non-active, disabled, external, guest, or other accounts are not used
- To monitor user rights that are restricted
ADAudit Plus helps you avoid the GPOs monitoring complexities with real-time pre-configured reports and auditing of the changes along with alerts within a Domain & OU. The advanced Group Policy settings real-time audit reports highlight the elusive change details, and also provide the old and new values of the modified attributes.
Event 608 applies to the following operating systems:
- Windows Server 2000
- Windows 2003 and XP
Corresponding event ID in Windows 2008 and Windows Vista is 4704
Explore Active Directory auditing and reporting with ADAudit Plus.
- By clicking 'Schedule a personalized demo' you agree to processing of personal data according to the Privacy Policy .
- Track User Administrators
- User Management Reports
- Insider Threat Detection
- Monitor User Logon Actions
- GPO Settings Auditing
- IT Compliance Auditing
- Windows Member Server Auditing
- Windows File Integrity Monitoring
- Security Eventlog Monitoring
- ADManager Plus Active Directory Management & Reporting
- ADAudit Plus Real-time Active Directory Auditing and UBA
- EventLog Analyzer Real-time Log Analysis & Reporting
- ADSelfService Plus Self-Service Password Management
- AD360 Integrated Identity & Access Management
- Log360 ( On-Premise | Cloud ) Comprehensive SIEM and UEBA
- AD Free Tools Active Directory FREE Tools
- Server Hardening Automation
- PAC – Policy Analysis Center
- IIS – Hardening Automation
- SQL – Hardening Automation
User Rights Assignment - User rights, User wrongs
What are user rights Assignment?
User rights assignments regulate access to computer and domain resources, with the ability to override permissions set on specific objects. Managed in Group Policy , each user right assignment has a constant name as well as a Group Policy name associated with it. The constant names are used when referring to the user right assignments in log events. In this section, they’re referred to as user rights, but they’re commonly known as privileges. Privileges are actions at the computer level that you can assign to users or groups.
User rights assignment is a vital part of IT security access and access control, referring to the permissions and privileges granted to individual users, or groups on a local computer or device level. These permissions dictate what actions users can perform on the system and what resources they can access.

Managed through either the local security policy or group policy settings, these settings define who can perform tasks such as logging on locally, making changes within the system such as the system time, accessing specific files or directories, shutting the system down and more.
Managing user rights assignment is vital for maintaining the security and integrity of Windows servers. By carefully controlling which users have access to which resources and what actions they can perform, administrators can reduce the risk of unauthorized access, data breaches, and other security incidents.
What user rights assignment allow you to do
Unlike file and folder permissions that control access to specific data, user rights govern what actions users can perform on a computer system. These special permissions go beyond basic access and determine a user’s ability to perform tasks as shown in the table below:
| Allow log on locally | Allows users to log on directly to the server |
| Change the system time | Allows users to change the system time on a computer |
| Shut down the system | Allows users to shut down the computer |
| Debug programs | Allows users to debug programs running on the computer |
| Manage auditing and security log | Allows users to view and manage security logs on a computer |
| Take ownership of files or other objects | Allows users to take ownership of files or other objects on a computer |
| Load and unload device drivers | Allows users to load or unload device drivers on a computer |
| Back up files and directories | Allows users to back up files and directories on a computer |
| Restore files and directories | Allows users to restore backed-up files and directories on a computer |
| Allow log on through | Allows users to manage remote access to a computer |
Why assign user rights?
User rights assignment act as the gatekeeper to the system, determining what is and is not allowed to access the system. If not correctly configured it can leave a system exposed to potential threats which have been known vulnerabilities in the past:
Privilege Escalation : In some cases, a vulnerability combined with a weak user rights assignment configuration could allow an attacker with some initial access to escalate their privileges to a higher level.
Unintended Access : Many services and applications require network access, if set too permissive an attacker on the network could potentially exploit that vulnerability to gain access to unauthorized information.
Assigning user rights on Windows servers is crucial for maintaining a secure, well-managed environment where access to resources is controlled, and users have the appropriate level of permissions to perform their duties effectively while minimizing security risks.
CIS Microsoft Windows Server 2019 Benchmark Hardening
Significance of rights and permissions
By allocating precise privileges to individual users based on their organizational roles or functions, it is possible to mitigate unauthorized access to sensitive data or restricted areas of a system. If designed well, users of a system have access only to resources they need to perform their job roles.
A system with predefined rights can increase efficiency, minimizing the need for a manager to manually assign individual rights and permissions and the chances of their being human error during configurations.
This also allows for greater scalability, giving a system the flexibility it needs to grow and evolve with a company through growth and restructuring phases. Additionally, each user has a unique customized experience specifically tailored to their needs and roles enhancing day to day activities.
How do user rights assignment work
Assigning user rights offers administrators more granular control over who can perform specific actions or access certain system resources. Taking advantage of the principle of least privilege, it implements a zero-trust approach, ensuring users only have the specific rights necessary to perform their tasks. This helps to minimize the potential impact of security breaches and maintain a more secure system through.
How to find user rights assignment?
To view and modify user rights assignments on a local system:
To view the current User Rights Assignment, open the Local Security Policy tool ( secpol.msc ) either via Start menu or Control Panel:
- Go to the Start Menu.
- Open Windows Administrative Tools.
- Go to Local Security Policy.
- Within the Local Security Policy application, navigate to Security Settings.
- Go to Local Policies.
- User Rights Assignments will be shown as follows:
- To view or modify the list of users and groups, that are assigned to a specific privilege/user right (column “ Policy “), select the item from the list and open the properties dialog:
To view and modify user rights assignments set by Domain Group Policy:
Below is a video explaining how to view and modify user rights assignment via Domain Group Policy:
CIS User Rights Assignment Security Policies
The Center for Internet Security (CIS) is a valuable resource for organizations providing a set of globally recognized best practices and security guidelines to help organizations bolster their security posture. CIS covers various aspects of system configuration, including user authentication, network access control, and user rights assignments.
Within user rights assignments there are 48 individual controls that need to be implemented based on the specific environment and deployment. However these settings are not a one-size-fits-all solution and must be configured individually along with the hundreds more security settings specifically to the needs of each system.
By carefully reviewing and implementing the relevant CIS controls, the overall security posture of a system can be significantly improved and make it more difficult for attackers to exploit vulnerabilities.

User Rights assignment best practices
Managing user rights is complex. Each user has multiple settings that control their actions, and these settings can impact other security measures across the system. Ensuring everything is configured correctly is crucial for robust system security.
Server hardening offers an effective solution. This process automates the configuration and ongoing reinforcement of security settings, reducing manual effort and safeguarding your system in today’s dynamic threat landscape.

Subscribe to Email Updates
- Center for Internet Security (20)
- Compliance (24)
- Configuration Settings (86)
- Domain Controller (3)
- PowerShell (7)
- Remote Desktop Protocol (4)
- Security Account Manager (5)
- Security Guides (16)
- Server Message Block (1)
- System Hardening (20)
- TLS SSL (4)
- Vulnerabilities (22)
You might be interested

Learn how our tools can help you with hardening
- First Name *
- Last Name *
- Job Title *
Experience a personalized demo
Privacy overview.
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| PHPSESSID | session | This cookie is native to PHP applications. The cookie is used to store and identify a users' unique session ID for the purpose of managing user session on the website. The cookie is a session cookies and is deleted when all the browser windows are closed. |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
| _GRECAPTCHA | 5 months 27 days | This cookie is set by Google. In addition to certain standard Google cookies, reCAPTCHA sets a necessary cookie (_GRECAPTCHA) when executed for the purpose of providing its risk analysis. |
| __cfduid | 1 month | The cookie is used by cdn services like CloudFare to identify individual clients behind a shared IP address and apply security settings on a per-client basis. It does not correspond to any user ID in the web application and does not store any personally identifiable information. |
| Cookie | Duration | Description |
|---|---|---|
| bcookie | 2 years | This cookie is set by linkedIn. The purpose of the cookie is to enable LinkedIn functionalities on the page. |
| lang | session | This cookie is used to store the language preferences of a user to serve up content in that stored language the next time user visit the website. |
| lidc | 1 day | This cookie is set by LinkedIn and used for routing. |
| __stidv | 1 year | This cookie is used by ShareThis. This cookie is used for sharing the content from the website to social networks. |
| Cookie | Duration | Description |
|---|---|---|
| YSC | session | This cookies is set by Youtube and is used to track the views of embedded videos. |
| _gat | 1 minute | This cookies is installed by Google Universal Analytics to throttle the request rate to limit the colllection of data on high traffic sites. |
| Cookie | Duration | Description |
|---|---|---|
| _ga | 2 years | This cookie is installed by Google Analytics. The cookie is used to calculate visitor, session, campaign data and keep track of site usage for the site's analytics report. The cookies store information anonymously and assign a randomly generated number to identify unique visitors. |
| _gid | 1 day | This cookie is installed by Google Analytics. The cookie is used to store information of how visitors use a website and helps in creating an analytics report of how the website is doing. The data collected including the number visitors, the source where they have come from, and the pages visted in an anonymous form. |
| __stid | 1 year | The cookie is set by ShareThis. The cookie is used for site analytics to determine the pages visited, the amount of time spent, etc. |
| Cookie | Duration | Description |
|---|---|---|
| bscookie | 2 years | This cookie is a browser ID cookie set by Linked share Buttons and ad tags. |
| IDE | 1 year 24 days | Used by Google DoubleClick and stores information about how the user uses the website and any other advertisement before visiting the website. This is used to present users with ads that are relevant to them according to the user profile. |
| test_cookie | 15 minutes | This cookie is set by doubleclick.net. The purpose of the cookie is to determine if the user's browser supports cookies. |
| VISITOR_INFO1_LIVE | 5 months 27 days | This cookie is set by Youtube. Used to track the information of the embedded YouTube videos on a website. |
| Cookie | Duration | Description |
|---|---|---|
| AnalyticsSyncHistory | 1 month | No description |
| CONSENT | 16 years 8 months 26 days 14 hours | No description |
| drift_campaign_refresh | 30 minutes | No description |
| fpestid | 1 year | No description |
| st_samesite | session | No description |
| UserMatchHistory | 1 month | Linkedin - Used to track visitors on multiple websites, in order to present relevant advertisement based on the visitor's preferences. |

- Device Configuration Guides
- logrhythm.com
EVID 4704, 4705 : User Right Assignment (Part 1) (Security)
Event details.
| Event Type | Audit Authentication Policy Change |
|---|---|
| Event Description | : A user right was assigned. : A user right was removed. |
| Event IDs | 4704, 4705 |
Log Fields and Parsing
This section details the log fields available in this log message type, along with values parsed for both LogRhythm Default and LogRhythm Default v2.0 policies. A value of "N/A" (not applicable) means that there is no value parsed for a specified log field.
| Log Field | LogRhythm Default | LogRhythm Default v2.0 | |
|---|---|---|---|
| Provider | N/A | N/A | |
| EventID | <vmid> | <vmid> | |
| Version | N/A | N/A | |
| Level | <severity> | <severity> | |
| Task | N/A | <vendorinfo> | |
| Opcode | N/A | N/A | |
| Keywords | <tag1> | <result> | |
| TimeCreated | N/A | N/A | |
| EventRecordID | N/A | N/A | |
| Correlation | N/A | N/A | |
| Execution | <processid> | N/A | |
| Channel | N/A | N/A | |
| Computer | <dname> | <dname> | |
| Event Data | <vendorinfo>, <subject> | N/A | |
| SubjectUserSid | <objectname> | N/A | |
| SubjectUserName | <login> | <login> | |
| SubjectDomainName | <domain> | <domainorigin> | |
| SubjectLogonId | <session> | <session> | |
| TargetSid | <account> | <domainimpacted>, <account> | |
| PrivilegeList | <object> | <subject> | |
Log Processing Settings
This section details log processing changes made from the LogRhythm Default policy to LogRhythm Default v2.0. In some cases, base rules are broken down into sub-rules to appropriately parse log message types by their event types.
LogRhythm Default
| Regex ID | ||||
|---|---|---|---|---|
| 1000628 | User Right Assignment | Base Rule | Privilege Granted | Access Granted |
| EVID 4704 : User Right Assigned | Sub Rule | Privilege Granted | Access Granted | |
| EVID 4705 : User Right Removed | Sub Rule | User Account Attribute Modified | Account Modified | |
| EVID 4717 : System Security Access Granted | Sub Rule | Access Granted Activity | Access Granted | |
| EVID 4718 : System Security Access Removed | Sub Rule | Access Revoked Activity | Access Revoked |
LogRhythm Default v2.0
| Regex ID | ||||
|---|---|---|---|---|
| 1011087 | V 2.0 : EVID 4704 & 4705 : User Rights Assignment | Base Rule | User Account Attribute Modified | Account Modified |
| V 2.0 : EVID 4704 : User Right Assigned | Sub Rule | User Account Attribute Modified | Account Modified | |
| V 2.0 : EVID 4705 : User Right Removed | Sub Rule | User Account Attribute Modified | Account Modified |
Please note, these errors can depend on your browser setup.
If this problem persists, please contact our support.
MyClassNotes
This blog contains notes from different learning sites. This notes falls in Information Security, Cyber Security, Network Security and other Security Domain class. Any suggestion to make this site helpful is truly welcome :)
Monday, September 30, 2019
User rights assignment in windows.
- Logon rights control who is authorized to log on to a computer and how they can log on.
- User rights permissions control access to computer and domain resources, and they can override permissions that have been set on specific objects.
| SeTcbPrivilege | Act as part of the operating system |
| SeMachineAccountPrivilege | Add workstations to domain |
| SeIncreaseQuotaPrivilege | Adjust memory quotas for a process |
| SeBackupPrivilege | Back up files and directories |
| SeChangeNotifyPrivilege | Bypass traverse checking |
| SeSystemtimePrivilege | Change the system time |
| SeCreatePagefilePrivilege | Create a pagefile |
| SeCreateTokenPrivilege | Create a token object |
| SeCreatePermanentPrivilege | Create permanent shared objects |
| SeDebugPrivilege | Debug programs |
| SeEnableDelegationPrivilege | Enable computer and user accounts to be trusted for delegation |
| SeRemoteShutdownPrivilege | Force shutdown from a remote system |
| SeAuditPrivilege | Generate security audits |
| SeIncreaseBasePriorityPrivilege | Increase scheduling priority |
| SeLoadDriverPrivilege | Load and unload device drivers |
| SeLockMemoryPrivilege | Lock pages in memory |
| SeSecurityPrivilege | Manage auditing and security log |
| SeSystemEnvironmentPrivilege | Modify firmware environment values |
| SeManageVolumePrivilege | Perform volume maintenance tasks |
| SeProfileSingleProcessPrivilege | Profile single process |
| SeSystemProfilePrivilege | Profile system performance |
| SeUndockPrivilege | Remove computer from docking station |
| SeAssignPrimaryTokenPrivilege | Replace a process level token |
| SeRestorePrivilege | Restore files and directories |
| SeShutdownPrivilege | Shut down the system |
| SeSyncAgentPrivilege | Synchronize directory service data |
| SeTakeOwnershipPrivilege | Take ownership of files or other objects |
No comments:
Post a comment.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Security policies were propagated with warning. 0x534 : No mapping between account names and security IDs was done.
Hello, we are getting many 1202 events. Security policies were propagated with warning. 0x534 : No mapping between account names and security IDs was done. When going through the suggested steps to find the problem account. It displayed domain admins. The full recommended steps are as follows: Security policies were propagated with warning. 0x534 : No mapping between account names and security IDs was done.
Advanced help for this problem is available on https://support.microsoft.com . Query for "troubleshooting 1202 events".
Error 0x534 occurs when a user account in one or more Group Policy objects (GPOs) could not be resolved to a SID. This error is possibly caused by a mistyped or deleted user account referenced in either the User Rights or Restricted Groups branch of a GPO. To resolve this event, contact an administrator in the domain to perform the following actions:
- Identify accounts that could not be resolved to a SID:
From the command prompt, type: FIND /I "Cannot find" %SYSTEMROOT%\Security\Logs\winlogon.log
The string following "Cannot find" in the FIND output identifies the problem account names.
Example: Cannot find JohnDough.
In this case, the SID for username "JohnDough" could not be determined. This most likely occurs because the account was deleted, renamed, or is spelled differently (e.g. "JohnDoe").
- Use RSoP to identify the specific User Rights, Restricted Groups, and Source GPOs that contain the problem accounts:
a. Start -> Run -> RSoP.msc b. Review the results for Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment and Computer Configuration\Windows Settings\Security Settings\Local Policies\Restricted Groups for any errors flagged with a red X. c. For any User Right or Restricted Group marked with a red X, the corresponding GPO that contains the problem policy setting is listed under the column entitled "Source GPO". Note the specific User Rights, Restricted Groups and containing Source GPOs that are generating errors.
- Remove unresolved accounts from Group Policy
a. Start -> Run -> MMC.EXE b. From the File menu select "Add/Remove Snap-in..." c. From the "Add/Remove Snap-in" dialog box select "Add..." d. In the "Add Standalone Snap-in" dialog box select "Group Policy" and click "Add" e. In the "Select Group Policy Object" dialog box click the "Browse" button. f. On the "Browse for a Group Policy Object" dialog box choose the "All" tab g. For each source GPO identified in step 2, correct the specific User Rights or Restricted Groups that were flagged with a red X in step 2. These User Rights or Restricted Groups can be corrected by removing or correcting any references to the problem accounts that were identified in step 1.
I am not clear on how to proceed with the last step 3 (g).
Windows Server A family of Microsoft server operating systems that support enterprise-level management, data storage, applications, and communications. 12,606 questions Sign in to follow
Hello @Computer Gladiator , How are things going on your end? Please keep me posted on this issue. If you have any further questions or concerns about this question, please let us know. I appreciate your time and efforts.
Best Regards, Daisy Zhou
do these errors typically cause a slowdown in network/internet connectivity from an end users pov? they are saying that the internet is super slow and outlook calendar is super slow. seeing alot of these 1202 events as well as 4098 related im sure.
They are bother removed and the event error has stopped appearing. Thank you.
Hello @Computer Gladiator ,
Thank you for your update. I am very glad that the information is helpful and the problem has been solved. As always, if there is any question in future, we warmly welcome you to post in this forum again. We are happy to assist you!
Tip: We may accept my first reply as answer, because that reply helps you and there are detailed steps to resolved the issue in that reply.Thank you very much.

6 additional answers
Thank you for posting here.
We can try the steps in the following link to see if we can find the account.
How to fix error “No mapping between account names and security IDs” in Active Directory https://www.rebeladmin.com/2016/01/how-to-fix-error-no-mapping-between-account-names-and-security-ids-in-active-directory/
Hope the information above is helpful. If anything is unclear, please feel free to let us know.
Tip: Please note: Information posted in the given link is hosted by a third party. Microsoft does not guarantee the accuracy and effectiveness of information.
Hello Daisy, in my case I see the problem at Computer Configuration > Security Settings > Restricted Groups. The groups names are Domain admins and Local admin. Not sure how they got there. Should these be removed?
Hello @Computer Gladiator ,
Thank you for your update.
If this group "Local admin" is custom group? Is it in AD now?
If this group "Local admin" is custom group and this group is not in AD, we can remove them to see if it helps.
Yes, Local Admin is a custom group and not a default group. I have removed it.

IMAGES
VIDEO
COMMENTS
Windows Security Log Event ID 4704. This event documents a change to user right assignments on this computer including the right and user or group that received the new right. Note: "User rights" and "privileges" are synonymous terms used interchangeably in Windows. Rights, like most other security settings, are defined in group policy objects ...
User rights are managed in Group Policy under the User Rights Assignment item. Each user right has a constant name and a Group Policy name associated with it. The constant names are used when referring to the user right in log events. You can configure the user rights assignment settings in the following location within the Group Policy ...
Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event. New Right: User Right [Type = UnicodeString]: the list of assigned user rights. This event generates only for user rights, not logon rights. Here is the list of possible user rights:
1 Press the Win + R keys to open Run, type secpol.msc into Run, and click/tap on OK to open Local Security Policy. 2 Expand open Local Policies in the left pane of Local Security Policy, and click/tap on User Rights Assignment. (see screenshot below step 3) 3 In the right pane of User Rights Assignment, double click/tap on the policy (ex: "Shut down the system") you want to add users and/or ...
undefined. User Rights Assignment is one of those meat and potatoes features of the operating system that we all have a cursory understanding of but rarely think about in depth. User rights include logon rights and permissions. Logon rights control who is authorized to log on to a device and how they can log on.
Event ID 4704 and event ID 4705 log the assignment or revocation of a user right, whereas Privilege Use events log the actual use of such rights. These two Policy Change events log the user or group that was the target of the change, as well as the system name of the right or rights that were assigned or revoked.
The User Rights Assignment section of Windows Policy is where you get to manage this stuff. To see for yourself, open the default domain controllers Group Policy Object (GPO) or run gpedit.msc. With the policy management window open, navigate to Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment.
Check User Rights How to get it. Get-UserRights.ps1 Direct Download Link or Personal File Server - Get-UserRights.ps1 Alternative Download Link or Personal File Server - Get-UserRights.txt Text Format Alternative Download Link. In order to check the Local User Rights, you will need to run the above (Get-UserRights), you may copy and paste the above script in your Powershell ISE and press play.
User Rights Assignment. Access Credential Manager as a trusted caller. Access this computer from the network. Act as part of the operating system. Add workstations to a domain. Adjust memory quotas for a process. Allow log on locally. Allow log on through Remote Desktop Services. Backup files and directories.
User rights. The following list describes a user right, identifies configuration settings that may cause issues, describes why you should apply the user right and why you may want to remove the user right, and provides examples of compatibility issues that may occur when the user right is configured. Access this computer from network. Background
608: User Right Assigned. On this page. This event documents a change to user right assignments on this computer. Rights, like most other security settings, are defined in group policy objects and applied by the computer. Therefore this event will normally show the Assigned By user as the system itself. To determine who actually made the rights ...
The default rights on a server for local built-in groups are set in the local security settings. To access the local security settings, click Start, type secpol.msc and hit enter. In the Local Security Policy editor, expand Local Policies, and click on User Rights Assignment. There you will see what groups/users are granted which rights.
The constant names are used when referring to the user right in log events. You can configure the user rights assignment settings in the following location within the Group Policy Management Console (GPMC) under Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment, or on the local computer by using the ...
On the Configuration settings page, as shown below in Figure 2, perform the following actions. Click Add settings and perform the following in Settings picker. Select User Rights as category. Select Allow Local Log On as setting. Specify the required users and local groups - all on separate lines - and click Next.
Chapter 10 Privilege Use Events You can use the Privilege Use audit category to track the exercise of user rights. Microsoft uses the terms privilege, right, and permission inconsistently. In the case of this audit category, privilege refers to most of the user rights that you find in the Local Security Policy under Security Settings\Local Policies\User Rights Assignment — with one important ...
If any accounts or groups other than the following are granted the "Create global objects" user right, this is a finding. - Administrators - Service - Local Service - Network Service For server core installations, run the following command: Secedit /Export /Areas User_Rights /cfg c:\path\filename.txt Review the text file.
Any change to the user rights assignment for an account becomes effective the next time the owner of the account logs on. Group Policy. This user right is defined in the Default Domain Controller Group Policy Object (GPO) and in the local security policy of workstations and servers.
I want to modify the user rights associated with a local user account.I want to add groups and users to a particular User Rights. This is done by opening the group policy and opening the following folder in the console tree: Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment.
Success Audit. When there is a change to the user rights assignments on a computer, Windows logs event ID 608. Rights that are defined in group policy objects are applied by the computer. The "User" field, meant to indicate the person who assigned or modified the rights, tends to show the name of the system. Thus, to determine the actual user ...
The constant names are used when referring to the user right assignments in log events. In this section, they're referred to as user rights, but they're commonly known as privileges. ... User Rights assignment best practices . ... The cookie is used to store and identify a users' unique session ID for the purpose of managing user session on ...
Regex ID Rule Name Rule Type Common Event Classification; 1011087: V 2.0 : EVID 4704 & 4705 : User Rights Assignment: Base Rule: User Account Attribute Modified: Account Modified: V 2.0 : EVID 4704 : User Right Assigned: Sub Rule: User Account Attribute Modified: Account Modified: V 2.0 : EVID 4705 : User Right Removed:
User rights are managed in Group Policy under the User Rights Assignment item. ... Event id 4704: A user right was assigned. Event id 4705: A user right was removed. The fact that should be kept in consideration is "User rights" and "privileges" are synonymous terms used interchangeably in Windows.
b. Review the results for Computer Configuration\Windows Settings\Security Settings\Local Policies\User Rights Assignment and Computer Configuration\Windows Settings\Security Settings\Local Policies\Restricted Groups for any errors flagged with a red X. c.